December 16, 2024By Prapattimynk
Improved Speed & Efficiency: Significantly faster and smoother DNS brute-forcing with lightweight resource usage. Memory & Resource Management: Optimized to handle large-scale DNS scans without consuming excessive system resources. Flexible Input: Supports both stdin and file-based domain lists for DNS brute-forcing. Concurrency Control: Rate limiting and concurrency management to ensure stable performance under heavy loads.
June 26, 2024By Prapattimynk
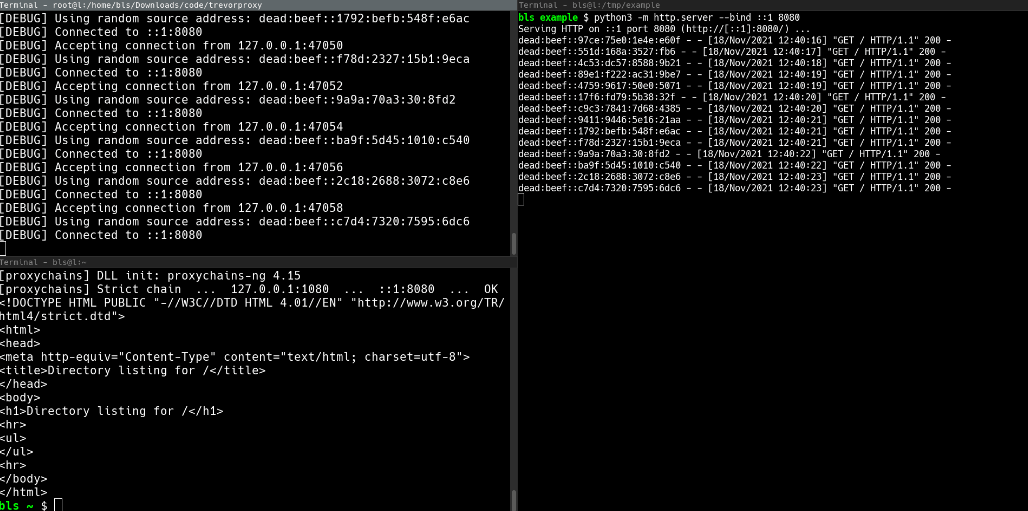
Installation pip install git+https://github.com/blacklanternsecurity/trevorproxy See the accompanying Blog Post for a fun rant and some cool demos! A SOCKS proxy written in Python that randomizes your source IP address. Round-robin your evil packets through SSH tunnels or give them billions of unique source addresses! TREVORproxy IPv6 Subnet Proxy Diagram TREVORproxy SSH Proxy Demo TREVORproxy Subnet
June 21, 2024By Prapattimynk
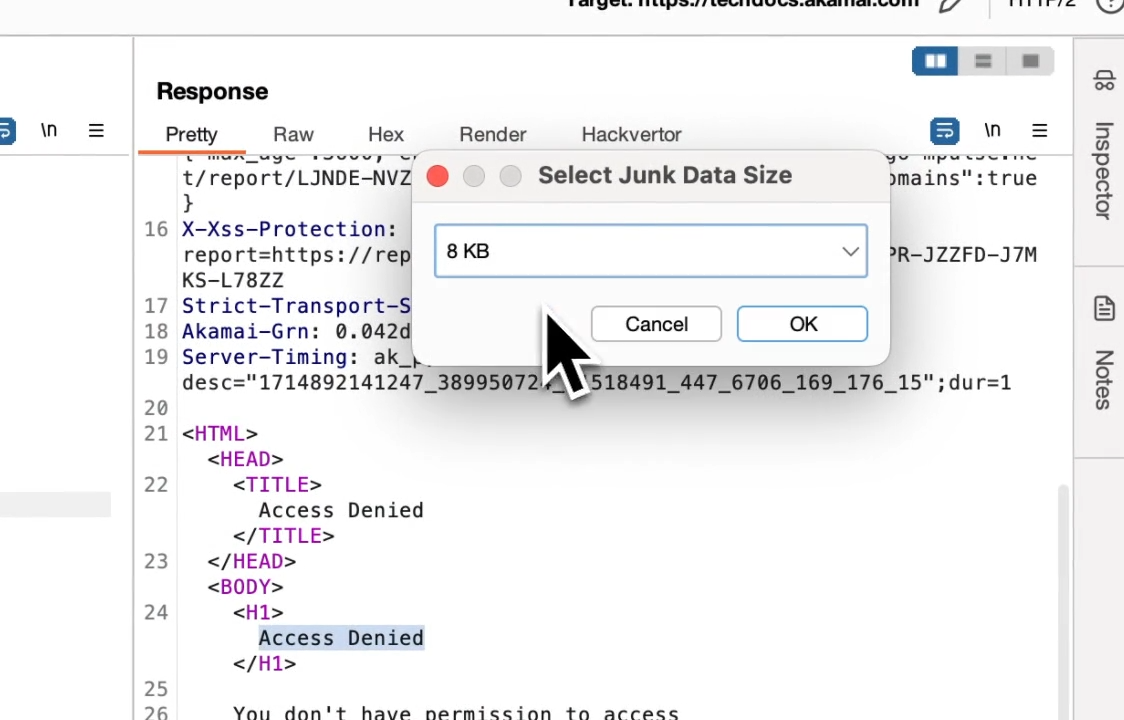
Most web application firewalls (WAFs) have limitations for how much data they can process when a request body is sent. This means for HTTP requests that contain a request body (i.e. POST, PUT, PATCH etc), it is usually possible to bypass the WAF by simply prepending junk data. When the request is padded with this
June 21, 2024By Prapattimynk
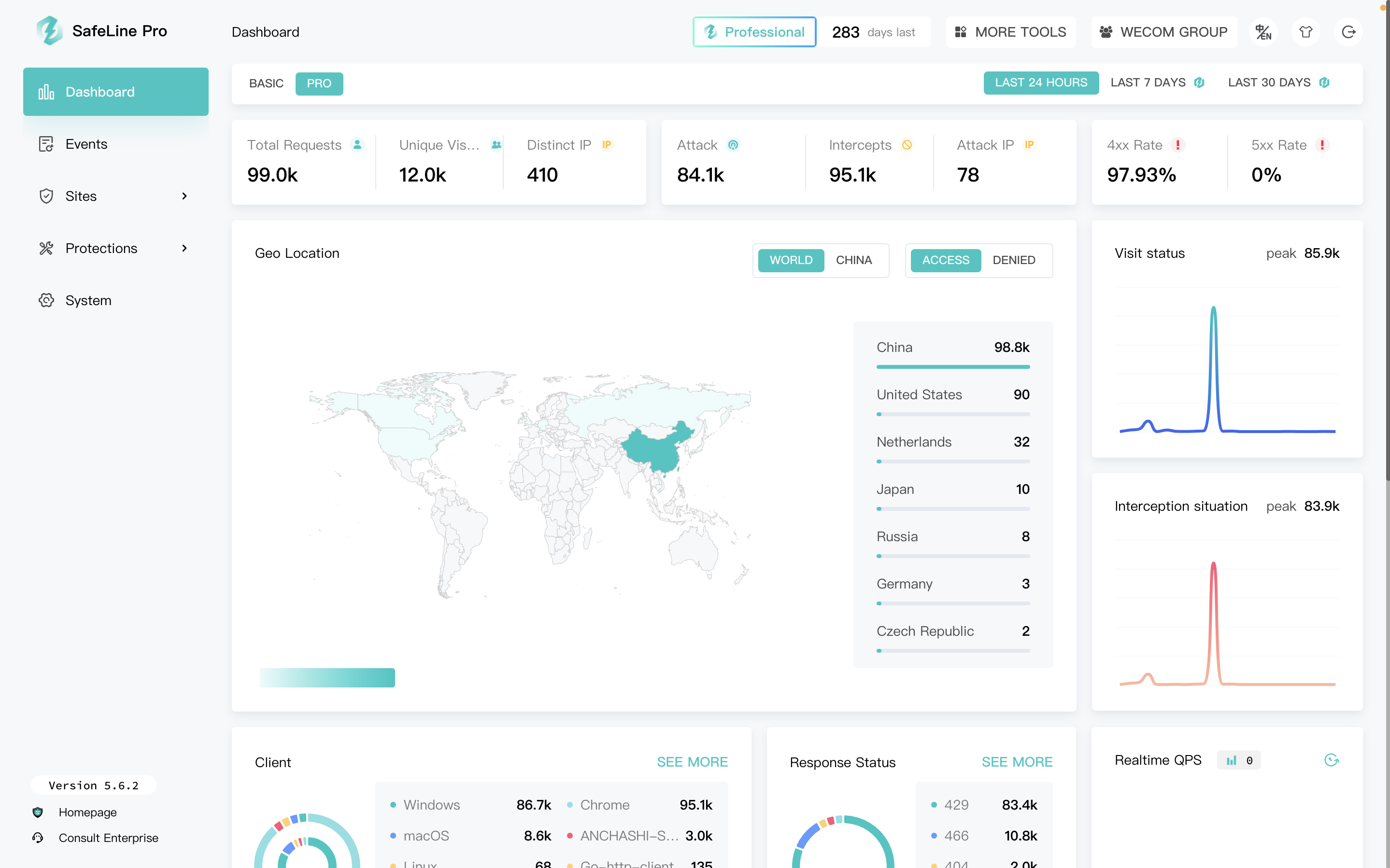
SafeLine is a web security gateway to protect your websites from attacks and exploits. It defenses for all of web attacks, such as sql injection, code injection, os command injection, CRLF injection, ldap injection, xpath injection, rce, xss, xxe, ssrf, path traversal, backdoor, bruteforce, http-flood, bot abused and so on. 🏠Home | 📖Documentation
June 18, 2024By Prapattimynk
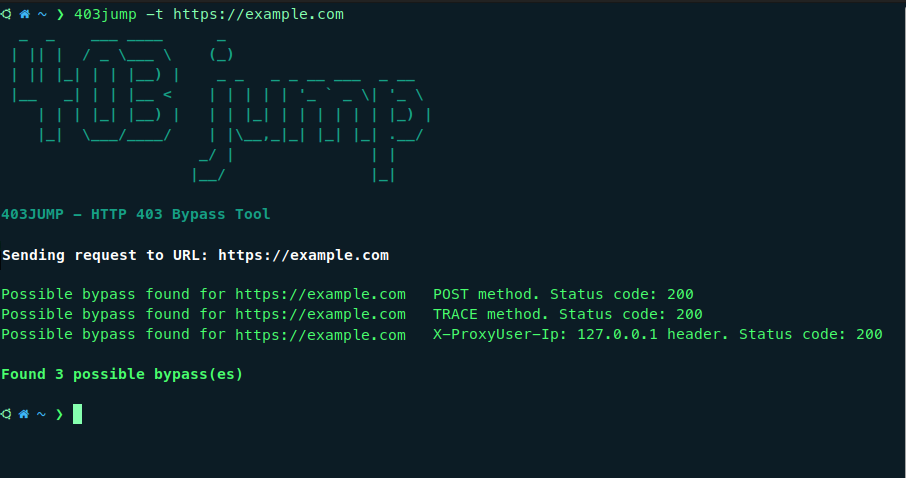
403JUMP is a tool designed for penetration testers and bug bounty hunters to audit the security of web applications. It aims to bypass HTTP 403 (Forbidden) pages using various techniques. Features Multiple Bypass Techniques Including: Different HTTP Verbs Different Headers Path Fuzzing. Customization: Allows customization of headers and cookies for more targeted testing. Concurrency: Performs
June 17, 2024By Prapattimynk
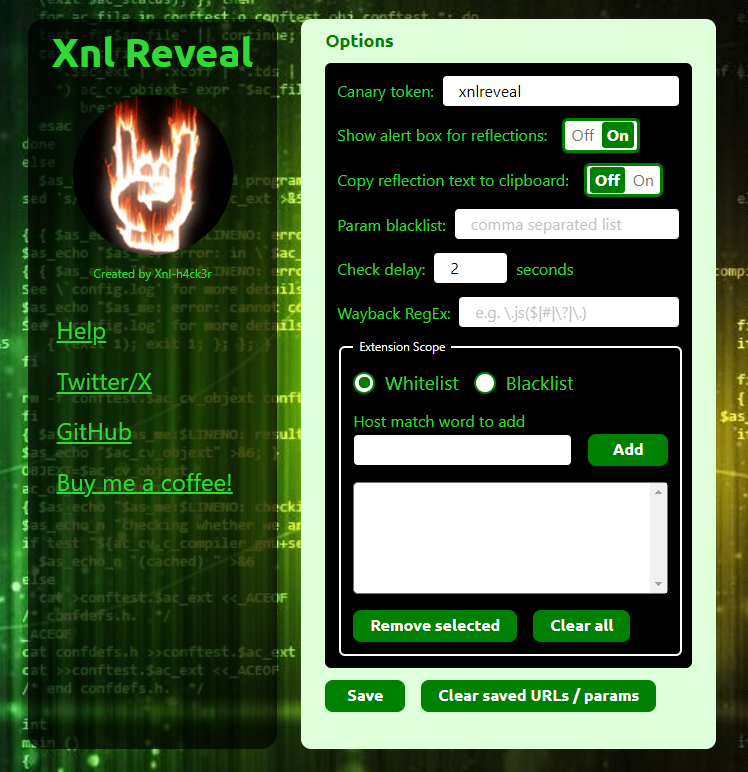
About – v3.6 This is a Chrome/Firefox Extension that can do the following: The ability to show an alert for reflected parameters was inspired by a comment by @renniepak on Episode 42 of the Critical Thinking – Bug Bounty Podcast where he mentioned he had his own browser extension that let him know about any
June 16, 2024By Prapattimynk
What is keyFinder? keyFinder is chrome extension that searches the DOM for any embedded script link, as script tag may contain keys for specific API(such as Google maps API) and you can add keywords to search for it at any website you visit. Features: it searches the DOM for “src” of scripts and see if
June 14, 2024By Prapattimynk
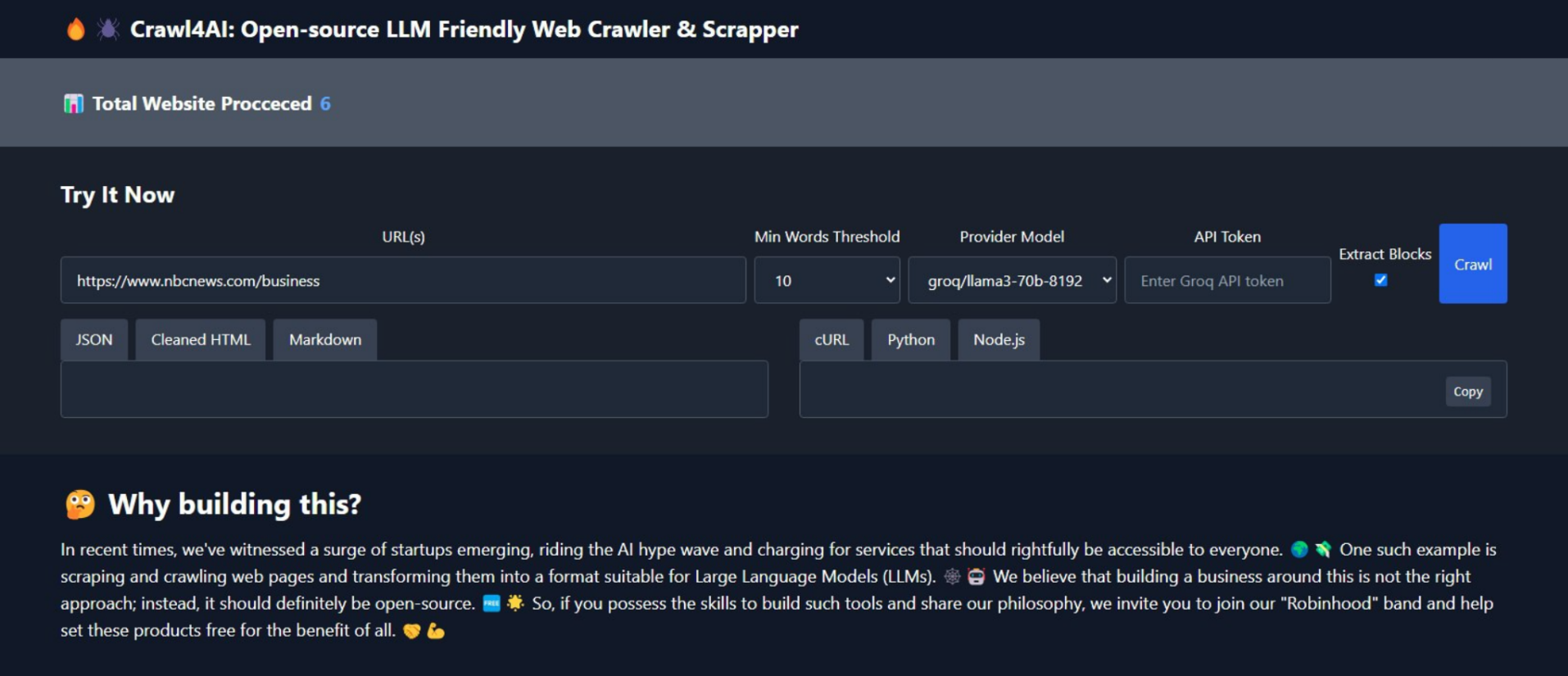
Crawl4AI v0.2.3 🕷️🤖 Crawl4AI has one clear task: to simplify crawling and extract useful information from web pages, making it accessible for large language models (LLMs) and AI applications. 🆓🌐 Use as REST API: Check Use as Python library: Recent Changes v0.2.3 🎨 Extract and return all media tags (Images, Audio, and Video). Check result.media
June 14, 2024By Prapattimynk
IconJector This is a Windows Explorer DLL injection technique that uses the change icon dialog on Windows. https://github.com/0xda568/IconJector/assets/61665703/bbf53775-ad8d-422b-b186-663ff5074976 How does it work? Firstly, a folder is created in the temp directory, and the properties of the folder are opened using SHObjectProperties. To retrieve the handle of the window independently of the system language, EnumWindows is
June 14, 2024By Prapattimynk
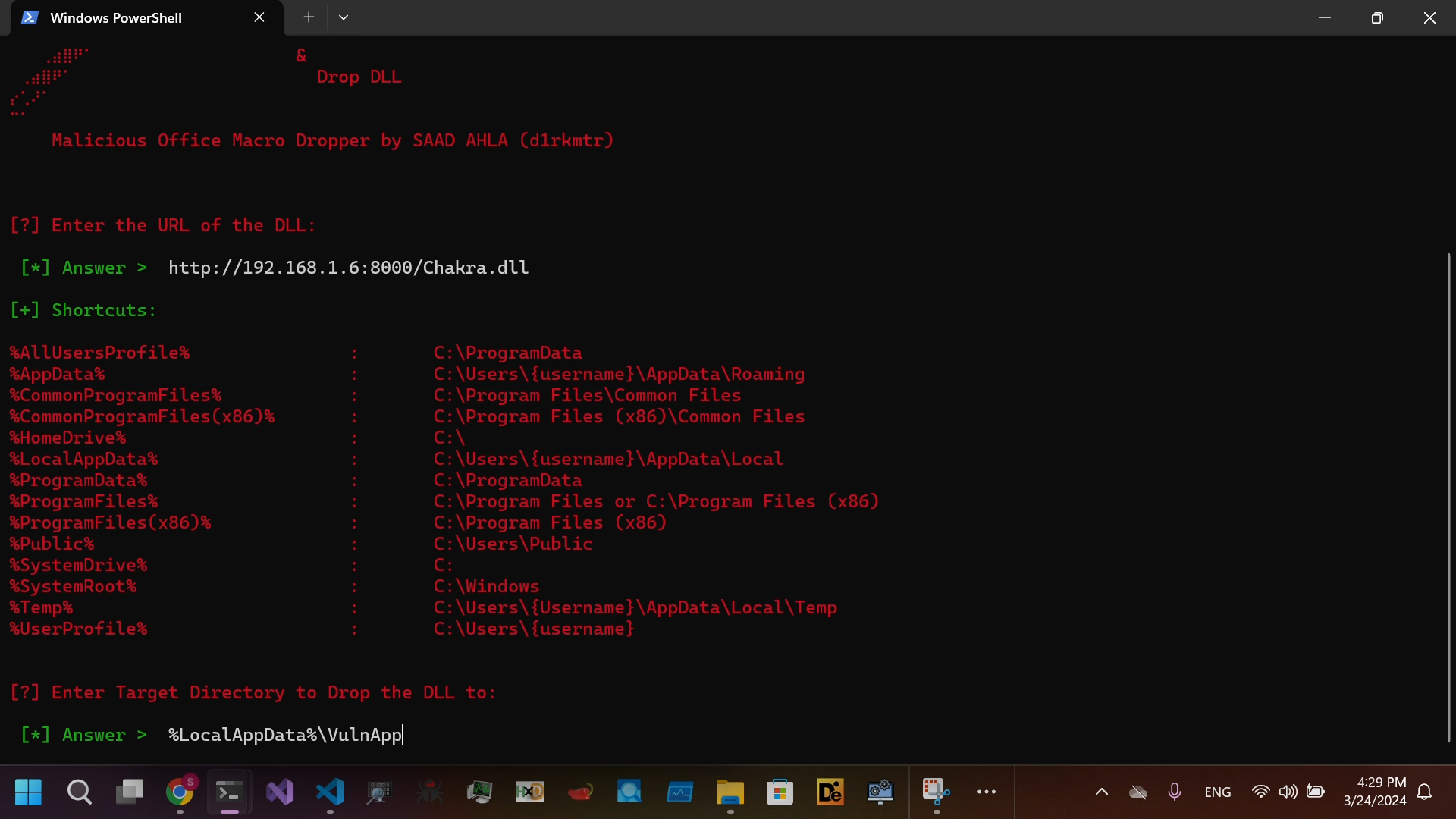
Project that generates Malicious Office Macro Enabled Dropper for DLL SideLoading and Embed it in Lnk file to bypass MOTW Install requirements pip install -r requirements.txt Video Demonstration https://github.com/SaadAhla/dropper/assets/123980007/7db05d2c-05e5-4a70-b967-6faecd7a296e Direct View On Github
April 27, 2024By Prapattimynk
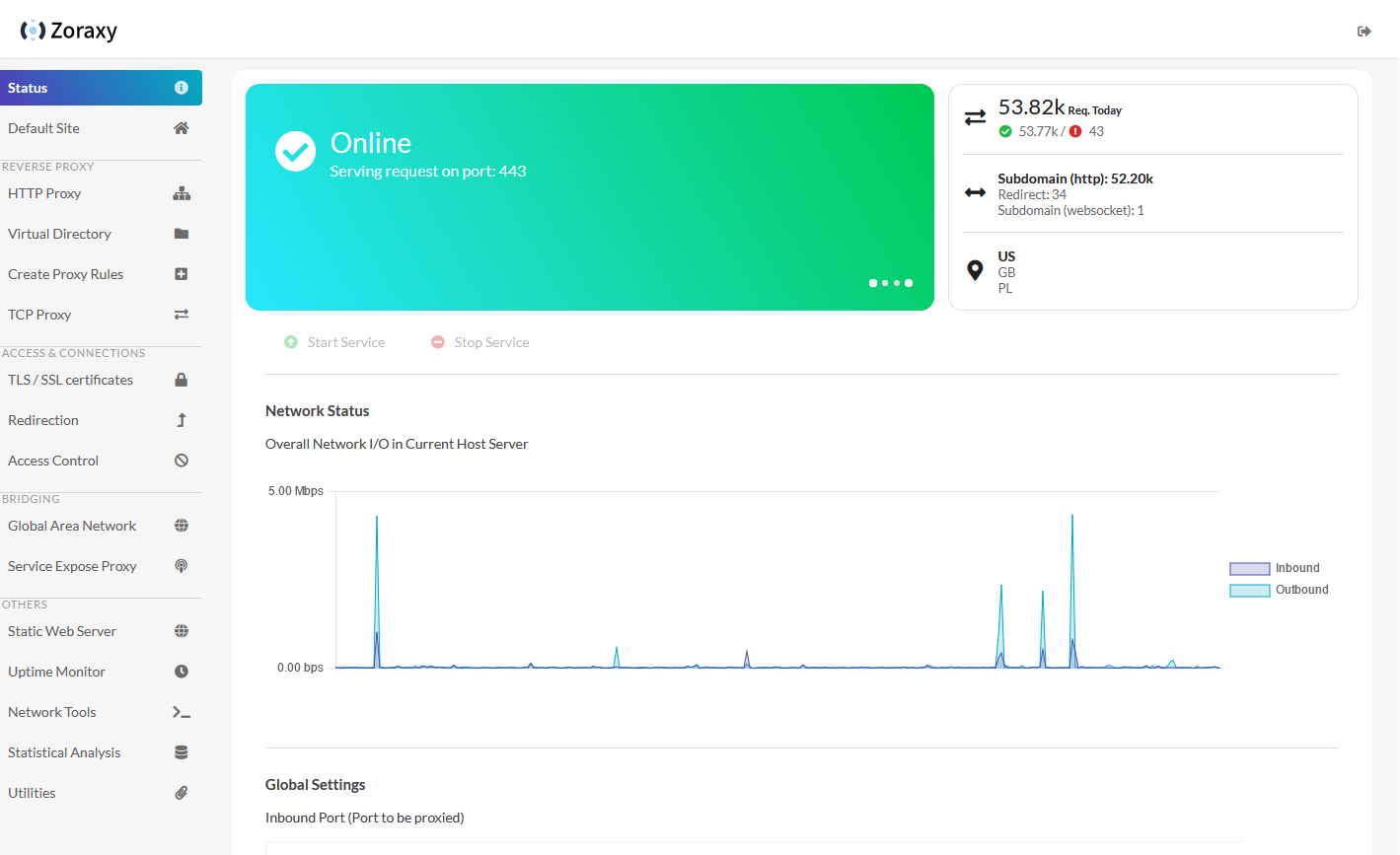
https://github.com/tobychui/zoraxy General purpose request (reverse) proxy and forwarding tool for networking noobs. Now written in Go! Zoraxy v3 HTTP proxy config is not compatible with the older v2. If you are looking for the legacy version of Zoraxy, take a look at the v2 branch Features Downloads Windows /Linux (amd64) /Linux (arm64) For other systems or architectures, please
April 4, 2024By Prapattimynk
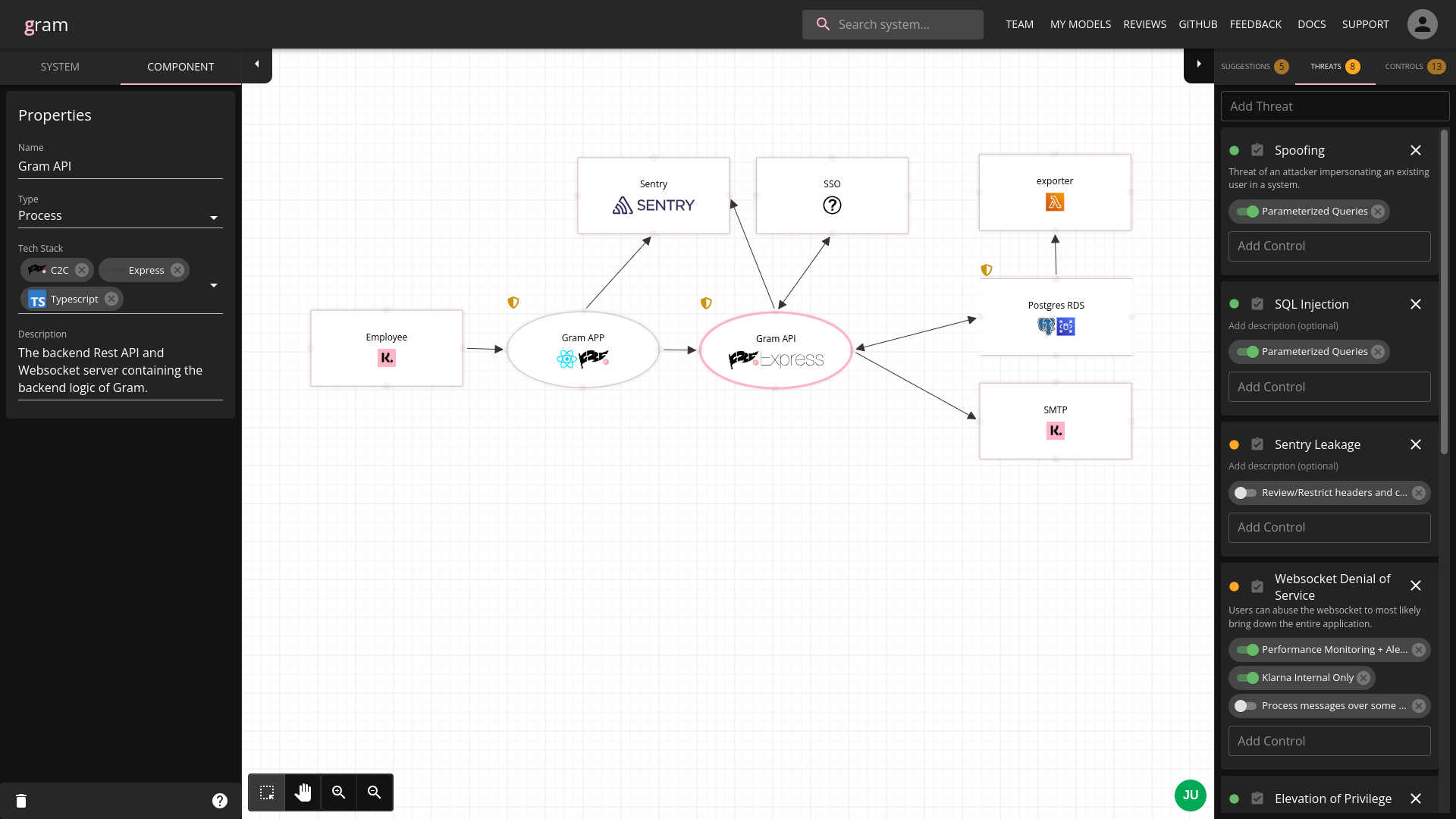
https://github.com/klarna-incubator/gram Gram is Klarna’s own threat model diagramming tool developed internally by Klarna’s Secure Development team. It is a webapp for engineers to collaboratively create threat models for their systems, providing a easy-to-understand way to document a system as a dataflow diagram with threats/controls attached. Features ✨ Getting Started 🚀 See Quick Start.
March 26, 2024By Prapattimynk
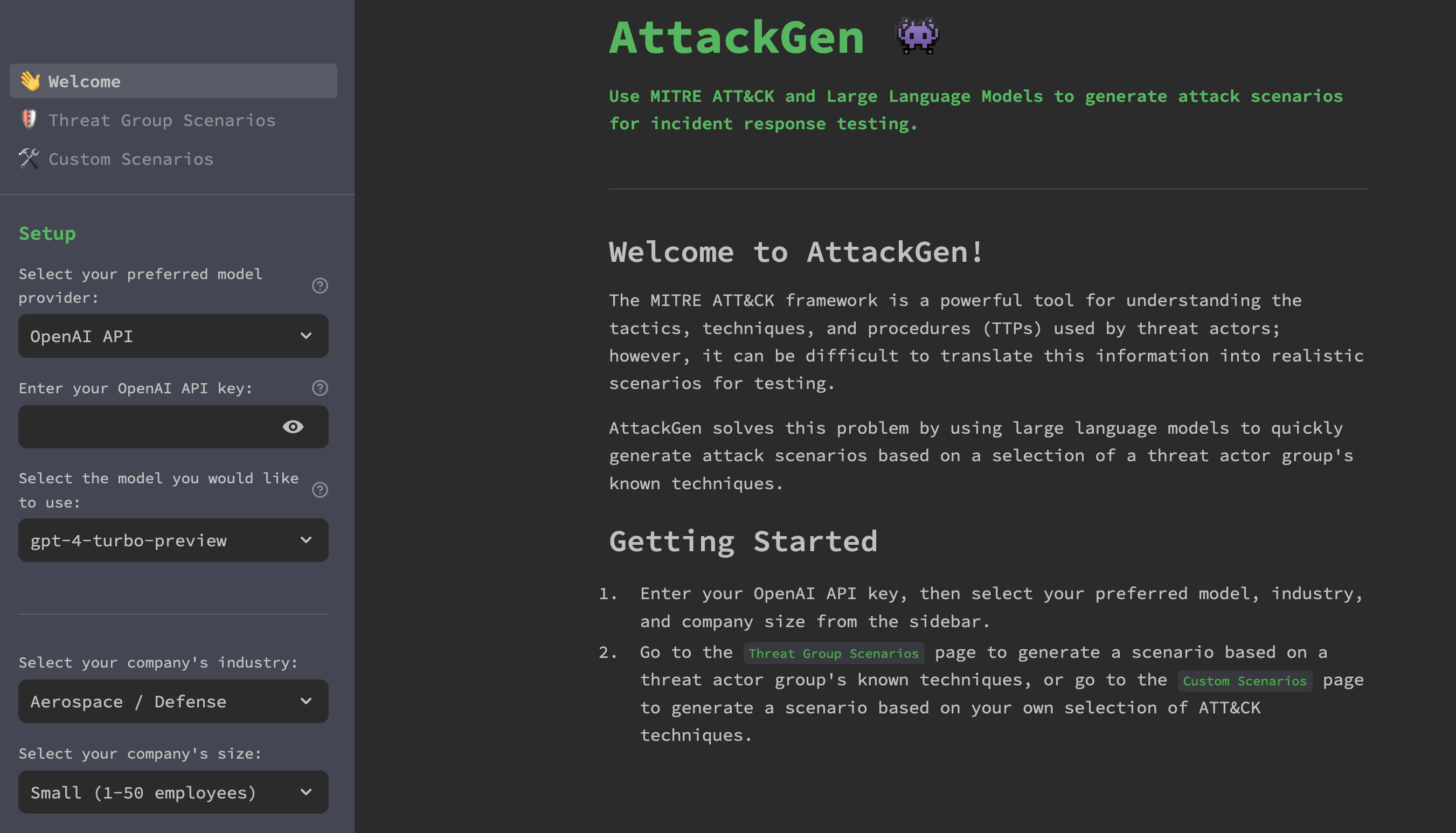
https://github.com/mrwadams/attackgen AttackGen is a cybersecurity incident response testing tool that leverages the power of large language models and the comprehensive MITRE ATT&CK framework. The tool generates tailored incident response scenarios based on user-selected threat actor groups and your organisation’s details. Features Requirements Installation Option 1: Cloning the Repository Option 2: Using Docker LangSmith Setup If
March 23, 2024By Prapattimynk
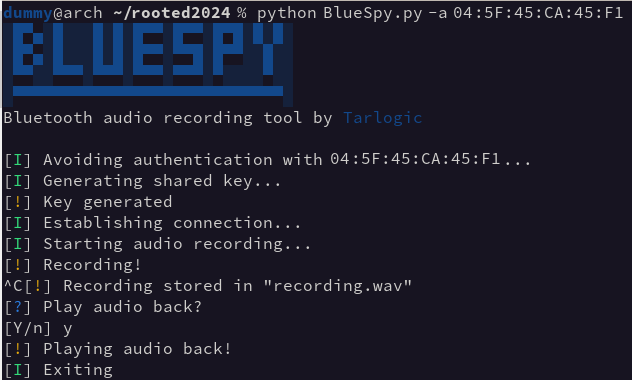
https://github.com/TarlogicSecurity/BlueSpy This repository contains the implementation of a proof of concept to record and replay audio from a bluetooth device without the legitimate user’s awareness. The PoC was demonstrated during the talk BSAM: Seguridad en Bluetooth at RootedCON 2024 in Madrid. It’s designed to raise awareness about the insecure use of Bluetooth devices, and the need of a consistent
March 11, 2024By Prapattimynk
https://github.com/d78ui98/APKDeepLens APKDeepLens is a Python based tool designed to scan Android applications (APK files) for security vulnerabilities. It specifically targets the OWASP Top 10 mobile vulnerabilities, providing an easy and efficient way for developers, penetration testers, and security researchers to assess the security posture of Android apps. Features APKDeepLens is a Python-based tool that performs
January 30, 2024By Prapattimynk
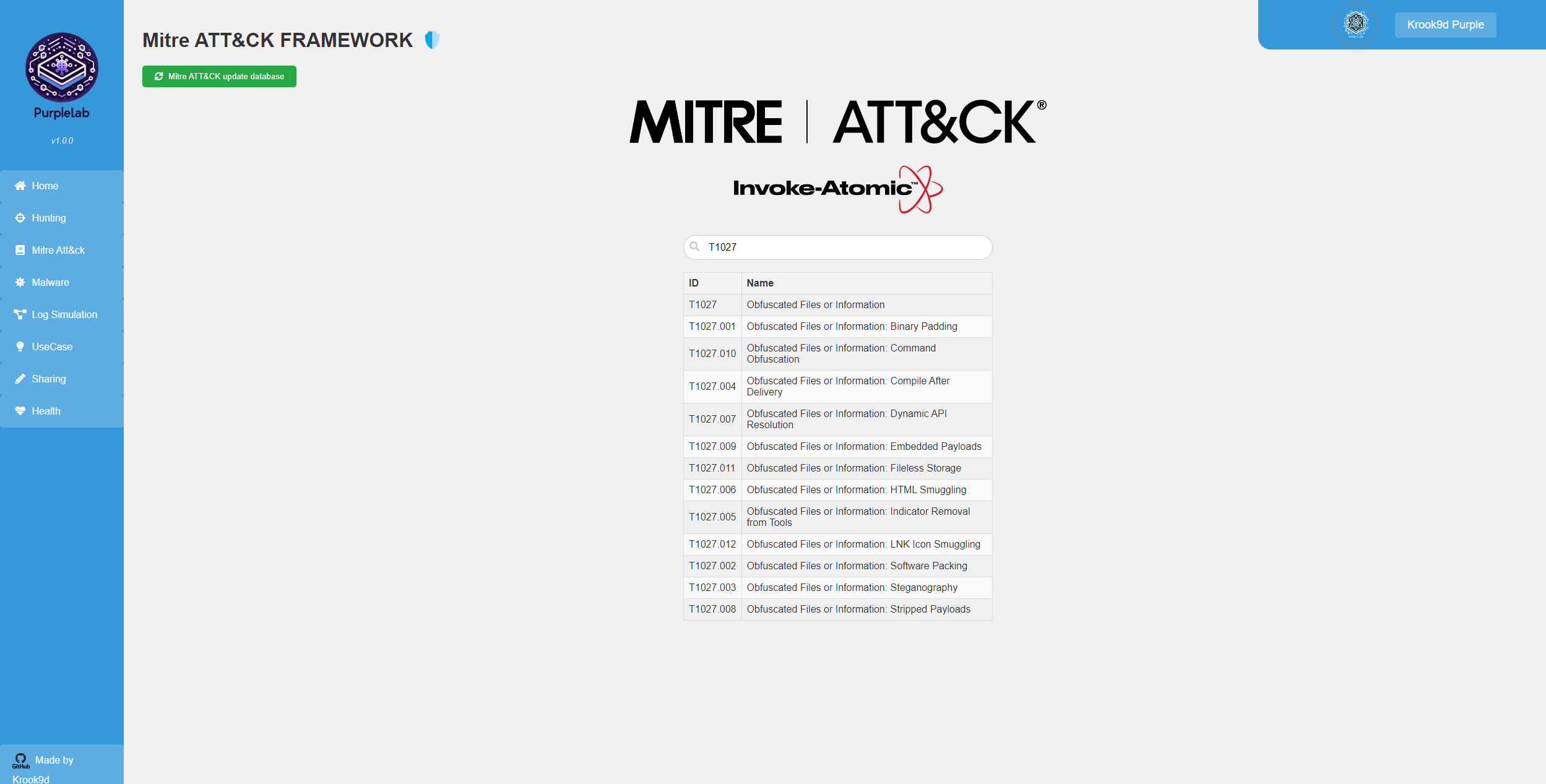
What is PurpleLab ? This solution will allow you to easily deploy an entire lab to create/test your detection rules, simulate logs, play tests, download and run malware and mitre attack techniques, restore the sandbox and many other features. https://github.com/Krook9d/PurpleLab The lab contains : Installation procedure ⚠️ To have a fully clean installation, you have to