As web application security remains a top priority, understanding the latest XSS (Cross-Site Scripting) hidden tools is essential for ensuring robust protection. In this blog post, we present a curated list of the top 10 XSS tools that security professionals and ethical hackers should know in 2023. These tools are designed to help identify and mitigate XSS vulnerabilities, ultimately fortifying web applications against potential attacks. Stay ahead of the game and explore these hidden gems to bolster your web application security arsenal.
What is XSS (Cross-Site-Scripting)
XSS (Cross-Site Scripting) is a type of security vulnerability that allows an attacker to inject malicious code into a trusted website. This code can then be executed by the website’s users, allowing the attacker to steal their data, hijack their session, or perform other malicious actions.
Here’s an example of how an XSS attack might work:
An attacker visits a website that allows users to post comments.
The attacker enters a malicious comment that contains JavaScript code.
The website’s code does not properly validate or escape the user input, so the malicious code is executed when another user visits the page and sees the comment.
The malicious code can then steal the user’s data, hijack their session, or perform other malicious actions.
There are two main types of XSS attacks:
- Reflected XSS attacks occur when the malicious code is reflected back to the user in the response from the web server. For example, this could happen if the website displays user comments without properly escaping them.
- Stored XSS attacks occur when the malicious code is stored on the web server and is then executed by other users who visit the page. For example, this could happen if the website allows users to save comments or other content that contains malicious code.
XSS attacks can be very difficult to prevent, but there are a number of things that website developers can do to mitigate the risk, such as:
Validating and escaping all user input before it is displayed on the page.
Using a web application firewall (WAF) to block known XSS attacks.
Keeping the website’s software up to date with the latest security patches.
If you think you may have been the victim of an XSS attack, there are a few things you can do:
Change your passwords for all of your online accounts, especially those that you used on the website where you may have been attacked.
Monitor your accounts for any unauthorized activity.
Report the attack to the website’s security team.
Top 10 XSS (Cross-Site-Scripting) Hidden Tools
In the world of web application security, staying updated with the latest tools and techniques is crucial to protect against vulnerabilities. XSS (Cross-Site Scripting) remains one of the most prevalent and potentially dangerous security flaws. To help security professionals and ethical hackers in their mission to secure web applications, we have compiled a list of the top 10 hidden XSS tools that you should be aware of in 2023. These tools are designed to identify and mitigate XSS vulnerabilities, ensuring safer and more robust web applications.
DOMinator
DOMinator is a powerful tool available on GitHub that focuses on detecting and exploiting DOM-based vulnerabilities, including DOM-based XSS (Cross-Site Scripting). It offers a unique approach to analyzing the Document Object Model (DOM) of web applications, which is crucial for understanding how JavaScript interacts with the DOM and potentially introduces security weaknesses.
TOOL – DOMinator
XSStrike
XSStrike is an open-source tool available on GitHub that specializes in detecting and exploiting XSS (Cross-Site Scripting) vulnerabilities in web applications. It offers a comprehensive suite of XSS scanning techniques and payloads, making it a valuable resource for security professionals and ethical hackers in their quest to secure web applications.
One notable feature of XSStrike is its ability to generate intelligent XSS payloads, encompassing a wide range of attack vectors and encoding techniques. By using these payloads, security experts can simulate real-world attack scenarios and determine the level of risk associated with discovered vulnerabilities.
TOOL – XSStrike
XSSer
XSSer is an open-source tool available on GitHub that focuses on finding and exploiting XSS (Cross-Site Scripting) vulnerabilities in web applications. It provides a command-line interface for security professionals and ethical hackers to identify and validate XSS vulnerabilities effectively.
One of the notable features of XSSer is its ability to generate reports detailing the discovered vulnerabilities, making it easier to understand and prioritize potential risks. The tool also provides options for fine-tuning the scanning process and adapting to various web application scenarios.
TOOL – XSSER
DalFox
Dalfox is an open-source tool available on GitHub that specializes in scanning web applications for XSS (Cross-Site Scripting) vulnerabilities. It provides security professionals and ethical hackers with a fast and efficient way to identify and exploit potential XSS weaknesses.
One notable feature of Dalfox is its ability to perform smart detection of reflected, stored, and DOM-based XSS vulnerabilities. By intelligently analyzing the application’s responses and interactions, Dalfox can identify potential points of XSS vulnerability and provide accurate results.
TOOL – DalFox
DSXS
DSXS (Damn Small XSS Scanner) is a powerful open-source tool available on GitHub that focuses on finding XSS (Cross-Site Scripting) vulnerabilities in web applications. Developed by a dedicated community of security enthusiasts, DSXS aims to streamline the process of identifying and mitigating XSS vulnerabilities, ensuring the robustness of web applications against potential attacks.
TOOL – DSXS
BruteXSS
BruteXSS is a powerful open-source XSS (Cross-Site Scripting) brute-force tool available on GitHub. Initially developed by Shawar Khan as a command-line interface (CLI) tool, it has been redesigned and enhanced with a graphical user interface (GUI) for added convenience.
Built using Python, BruteXSS is a cross-platform tool that can be run on various operating systems as long as Python is installed on the machine. This flexibility makes it accessible to a wider range of security professionals and ethical hackers.
TOOL – BruteXSS
XSScrapy
XSScrapy is an open-source tool available on GitHub that focuses on automating the process of finding XSS (Cross-Site Scripting) vulnerabilities in web applications. Developed by security enthusiasts, XSScrapy provides security professionals and ethical hackers with a powerful framework to systematically scan and identify potential XSS weaknesses.
One of the key features of XSScrapy is its ability to generate detailed reports, providing an overview of the discovered vulnerabilities and their associated details. These reports aid in the prioritization and mitigation of XSS risks, enabling security professionals to address the vulnerabilities effectively.
TOOL – XSScrapy
Wapiti
Wapiti is a widely used open-source web application vulnerability scanner available on GitHub. Developed in Python, Wapiti is designed to identify security vulnerabilities in web applications by performing a comprehensive and systematic scanning process.
With its versatile scanning capabilities, Wapiti can analyze various aspects of web applications, including input fields, URL parameters, and forms. It employs a wide range of techniques, such as fuzzing, to detect potential vulnerabilities like XSS (Cross-Site Scripting), SQL injection, and file inclusion.
TOOL – Wapiti
XSSFuzzer
XSS Fuzzer is a powerful tool used to test and identify XSS (Cross-Site Scripting) vulnerabilities in web applications. By generating a variety of malicious payloads and injecting them into different input fields and parameters, the XSS Fuzzer aims to discover potential weaknesses that can be exploited by attackers.
One of the key features of the XSS Fuzzer is its ability to generate customizable payloads. Users can define and modify the payloads according to their specific requirements, allowing for tailored testing of different XSS attack vectors. Additionally, the tool provides options to adjust parameters such as the depth of scanning, target URLs, and injection points, enabling comprehensive testing across various parts of the web application.
TOOL – XSSFuzzer
Burp Intruder
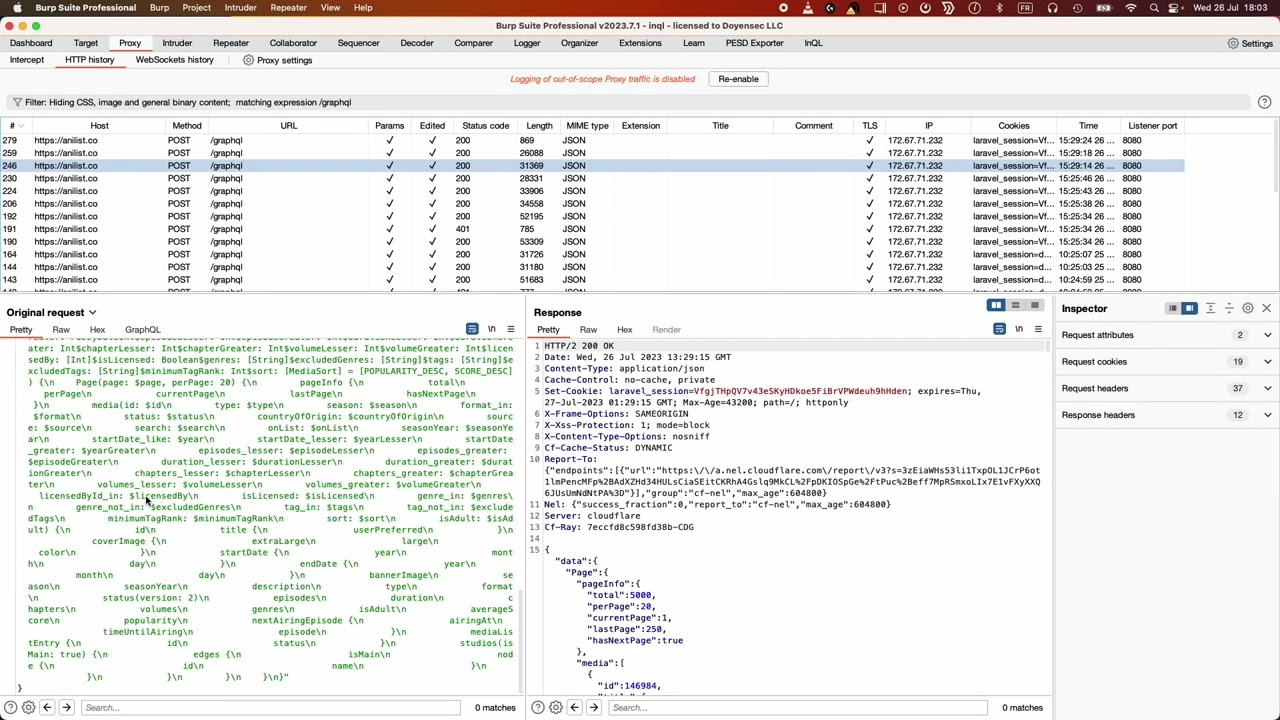
Burp Intruder is a widely recognized and powerful tool in the field of web application security testing. It is a module within the Burp Suite, a comprehensive set of tools designed for assessing the security of web applications.
Burp Intruder provides extensive functionality for automating and customizing various types of attacks, including brute-forcing, fuzzing, and injection testing. Its versatility makes it a valuable asset for security professionals, ethical hackers, and penetration testers.
With Burp Intruder, users can perform targeted attacks by specifying the desired injection points and defining custom payloads. It supports multiple attack types, such as time-based attacks, error-based attacks, and cluster bomb attacks, to uncover different classes of vulnerabilities.
TOOL – Burpsuite
Conclusion
In conclusion, XSS (Cross-Site Scripting) remains a prevalent and potentially dangerous vulnerability in web applications, making it essential for security professionals and developers to stay up-to-date with the latest tools and techniques for effective testing and mitigation. In this blog, we explored the top 10 hidden XSS tools that you should know in 2023.
These tools offer a range of features and capabilities, empowering security researchers, penetration testers, and developers to identify and address XSS vulnerabilities. From powerful scanners like XSStrike and Wapiti to automation tools like Burp Intruder and BruteXSS, each tool brings its unique approach to XSS testing.
We also delved into specialized tools like DOMinator, XSStrike, XXSer, Dalfox, and DSXS, each catering to specific XSS testing requirements and offering advanced techniques to uncover hidden vulnerabilities. Additionally, we explored the GUI redesign of BruteXSS, providing a more user-friendly experience.
The availability of these tools on GitHub, an open-source platform, encourages collaboration and continuous improvement. Developers and security enthusiasts contribute to their development, ensuring they remain effective against evolving XSS threats.
However, it’s crucial to remember that responsible and ethical usage of these tools is paramount. Prior authorization and consent from application owners are essential before conducting any security testing.
By leveraging the top 10 XSS hidden tools covered in this blog, security professionals can enhance their XSS testing capabilities, fortify web applications, and protect users’ sensitive information from potential attacks. Stay informed, keep exploring, and stay vigilant to combat XSS vulnerabilities in the dynamic and ever-evolving world of web application security.














What do you think?
Show comments / Leave a comment