December 16, 2024By Prapattimynk
Improved Speed & Efficiency: Significantly faster and smoother DNS brute-forcing with lightweight resource usage. Memory & Resource Management: Optimized to handle large-scale DNS scans without consuming excessive system resources. Flexible Input: Supports both stdin and file-based domain lists for DNS brute-forcing. Concurrency Control: Rate limiting and concurrency management to ensure stable performance under heavy loads.
June 26, 2024By Prapattimynk
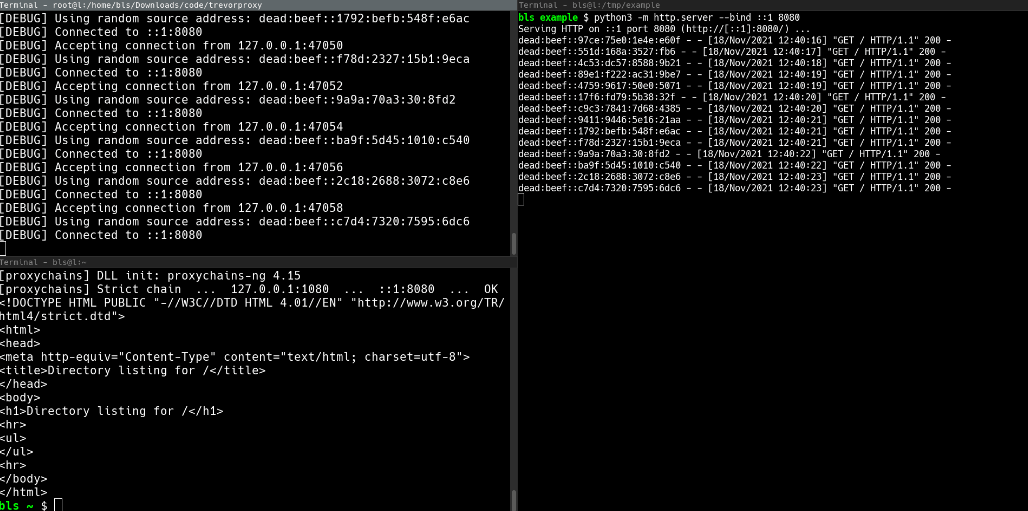
Installation pip install git+https://github.com/blacklanternsecurity/trevorproxy See the accompanying Blog Post for a fun rant and some cool demos! A SOCKS proxy written in Python that randomizes your source IP address. Round-robin your evil packets through SSH tunnels or give them billions of unique source addresses! TREVORproxy IPv6 Subnet Proxy Diagram TREVORproxy SSH Proxy Demo TREVORproxy Subnet
June 21, 2024By Prapattimynk
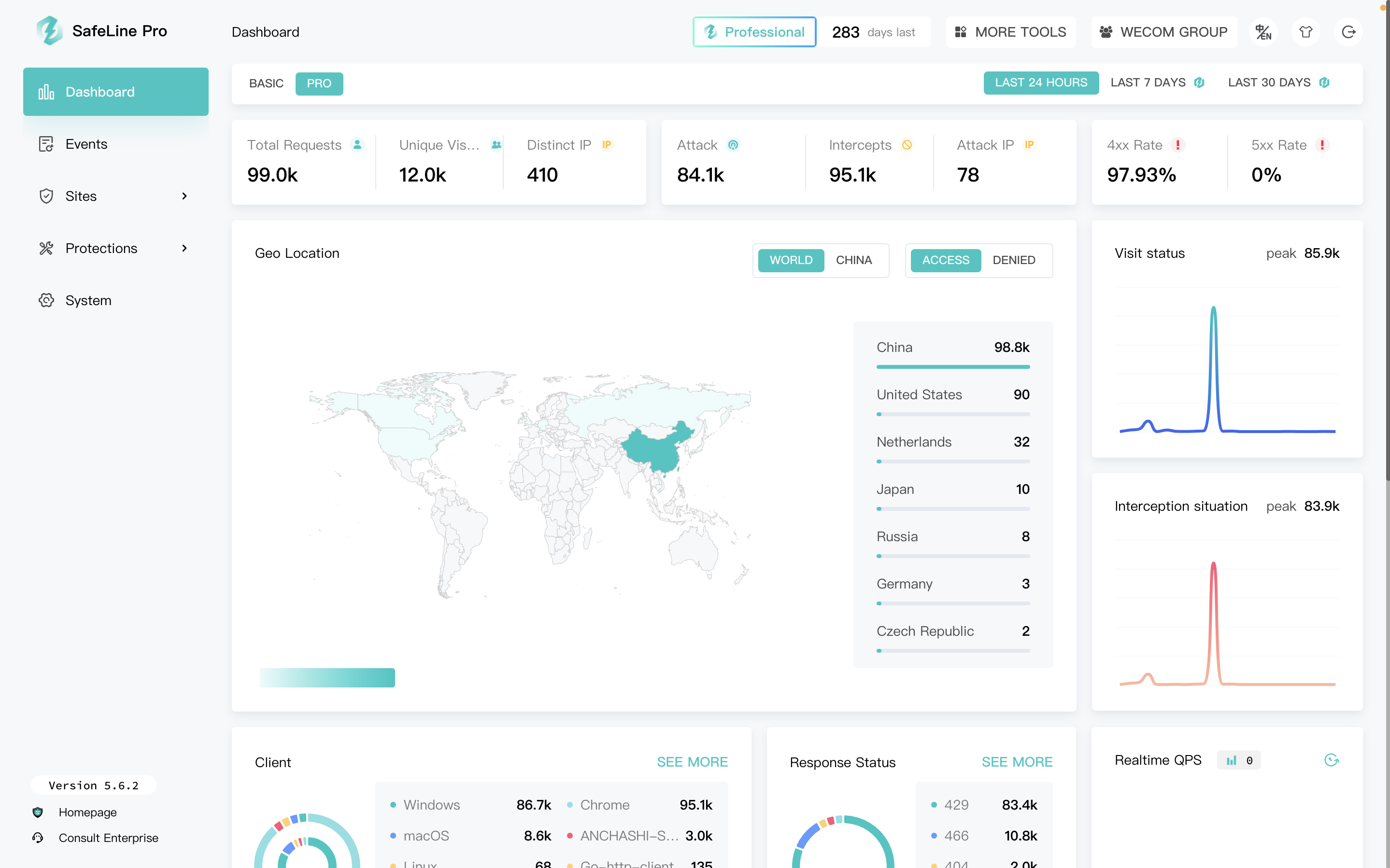
SafeLine is a web security gateway to protect your websites from attacks and exploits. It defenses for all of web attacks, such as sql injection, code injection, os command injection, CRLF injection, ldap injection, xpath injection, rce, xss, xxe, ssrf, path traversal, backdoor, bruteforce, http-flood, bot abused and so on. 🏠Home | 📖Documentation
June 21, 2024By Prapattimynk
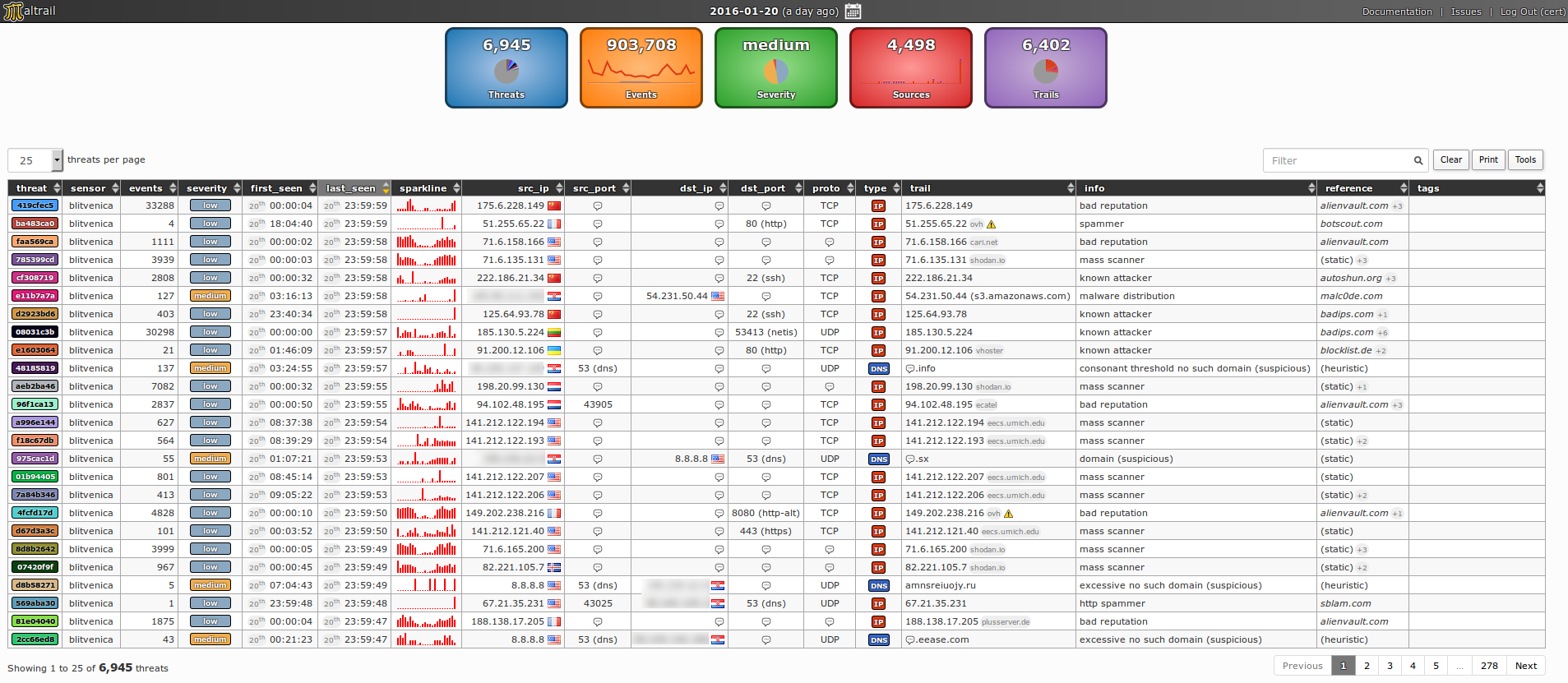
Content Introduction Architecture Demo pages Requirements Quick start Administrator’s guide Sensor Server User’s guide Reporting interface Real-life cases Mass scans Anonymous attackers Service attackers Malware Suspicious domain lookups Suspicious ipinfo requests Suspicious direct file downloads Suspicious HTTP requests Port scanning DNS resource exhaustion Data leakage False positives Best practice(s) License Sponsors Developers Presentations Publications Blacklist
April 27, 2024By Prapattimynk
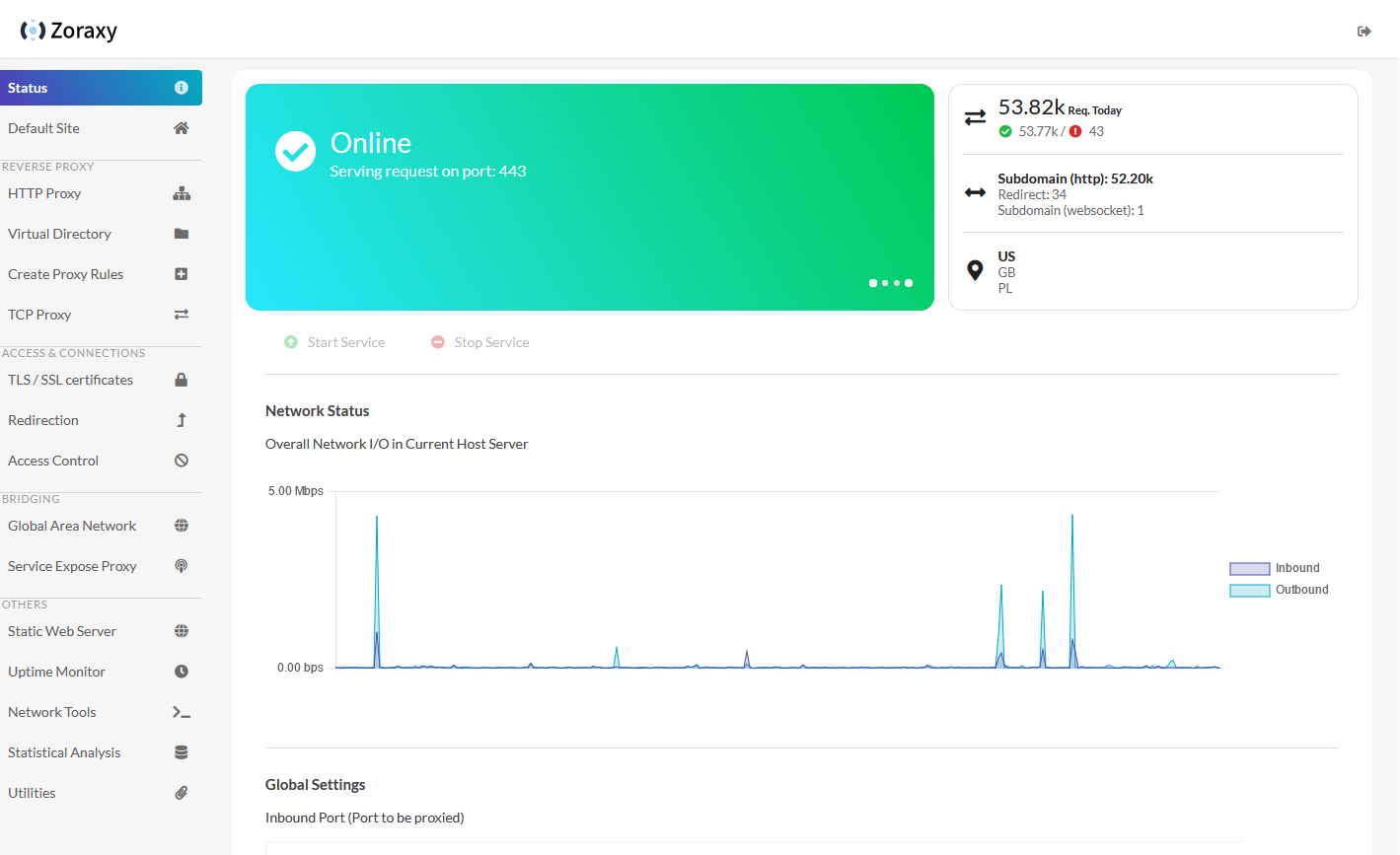
https://github.com/tobychui/zoraxy General purpose request (reverse) proxy and forwarding tool for networking noobs. Now written in Go! Zoraxy v3 HTTP proxy config is not compatible with the older v2. If you are looking for the legacy version of Zoraxy, take a look at the v2 branch Features Downloads Windows /Linux (amd64) /Linux (arm64) For other systems or architectures, please
March 26, 2024By Prapattimynk
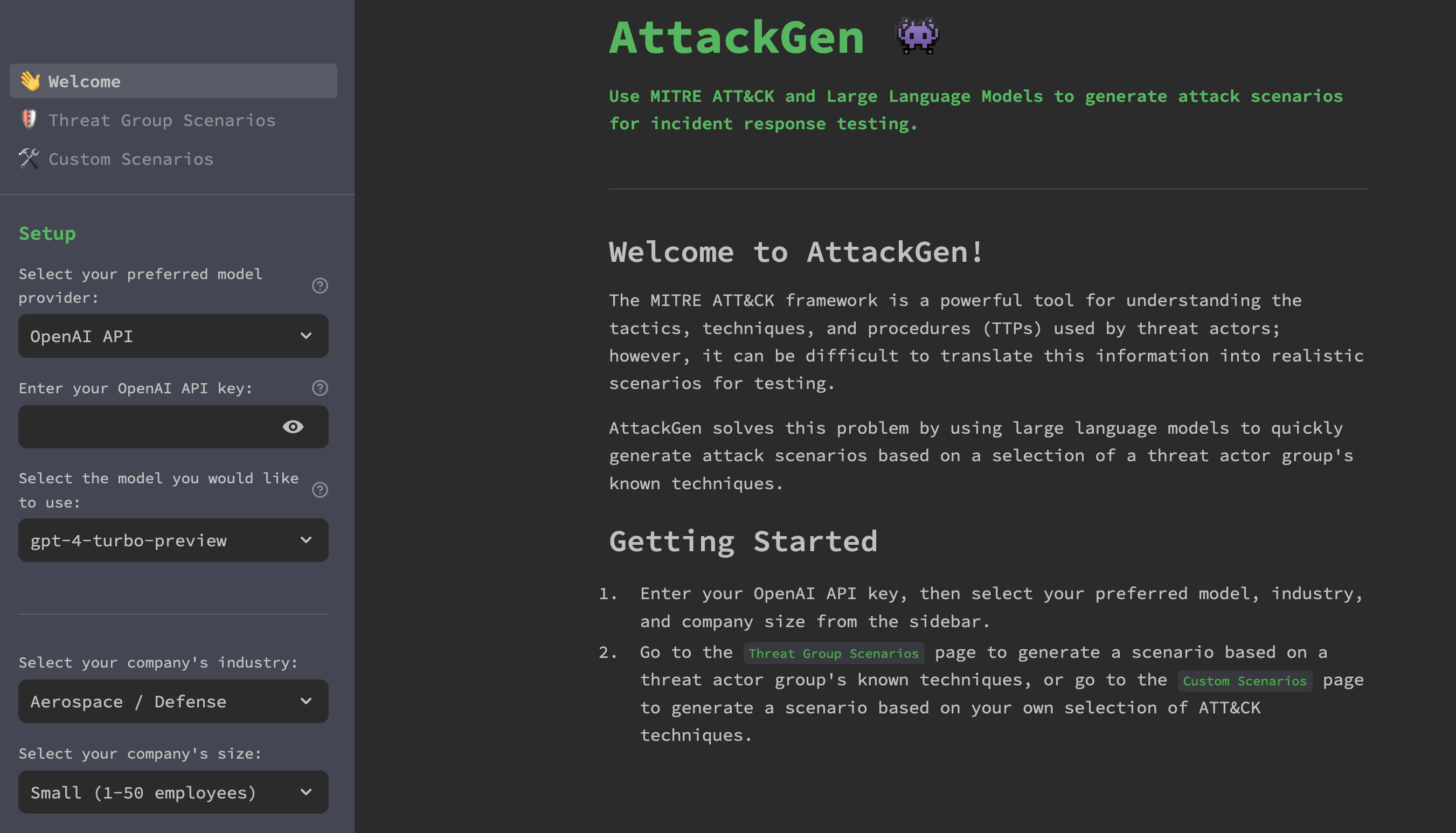
https://github.com/mrwadams/attackgen AttackGen is a cybersecurity incident response testing tool that leverages the power of large language models and the comprehensive MITRE ATT&CK framework. The tool generates tailored incident response scenarios based on user-selected threat actor groups and your organisation’s details. Features Requirements Installation Option 1: Cloning the Repository Option 2: Using Docker LangSmith Setup If
March 23, 2024By Prapattimynk
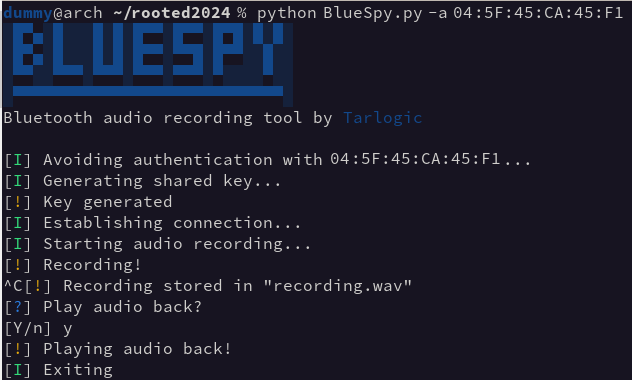
https://github.com/TarlogicSecurity/BlueSpy This repository contains the implementation of a proof of concept to record and replay audio from a bluetooth device without the legitimate user’s awareness. The PoC was demonstrated during the talk BSAM: Seguridad en Bluetooth at RootedCON 2024 in Madrid. It’s designed to raise awareness about the insecure use of Bluetooth devices, and the need of a consistent
January 30, 2024By Prapattimynk
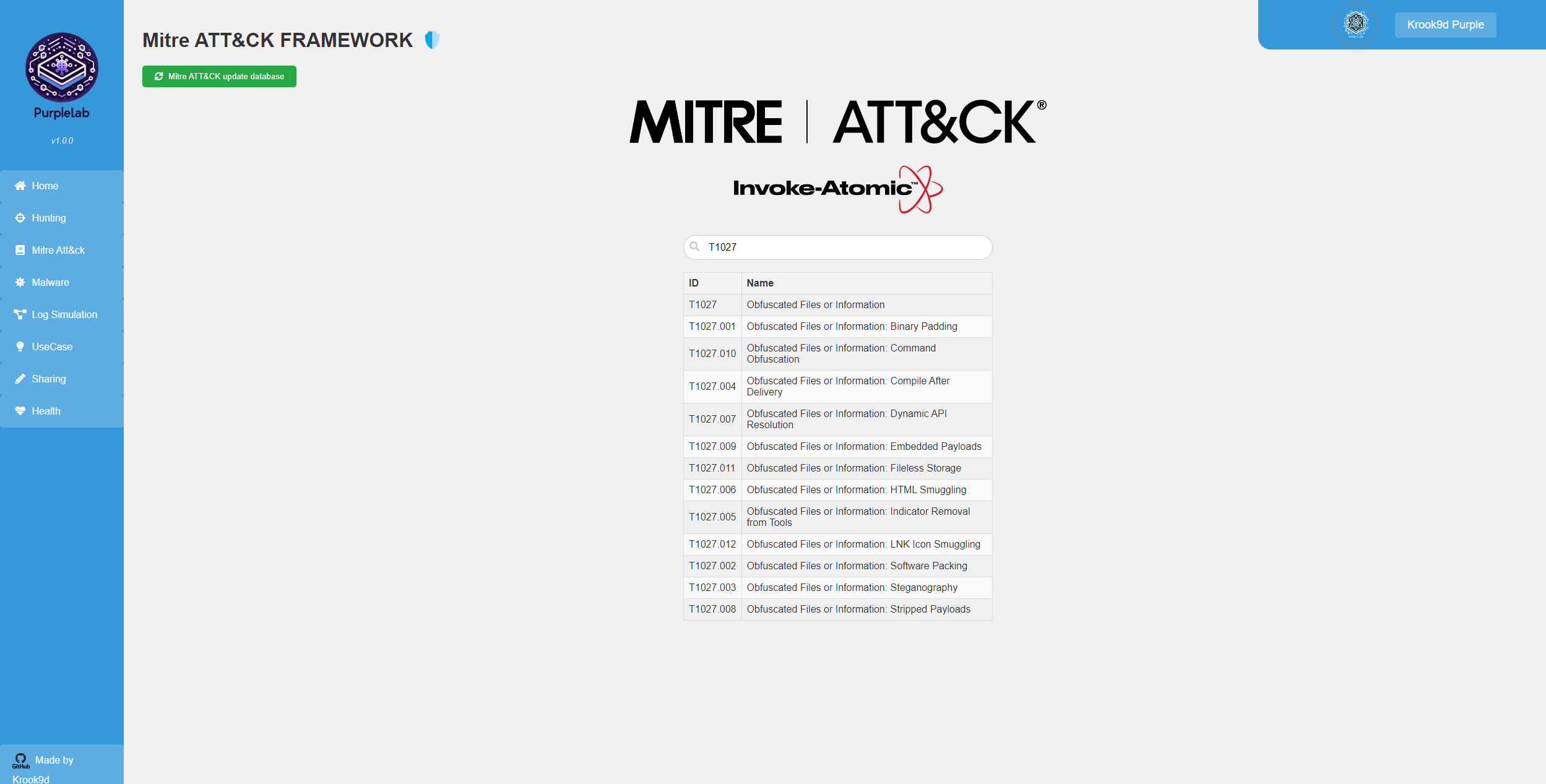
What is PurpleLab ? This solution will allow you to easily deploy an entire lab to create/test your detection rules, simulate logs, play tests, download and run malware and mitre attack techniques, restore the sandbox and many other features. https://github.com/Krook9d/PurpleLab The lab contains : Installation procedure ⚠️ To have a fully clean installation, you have to
January 28, 2024By Prapattimynk
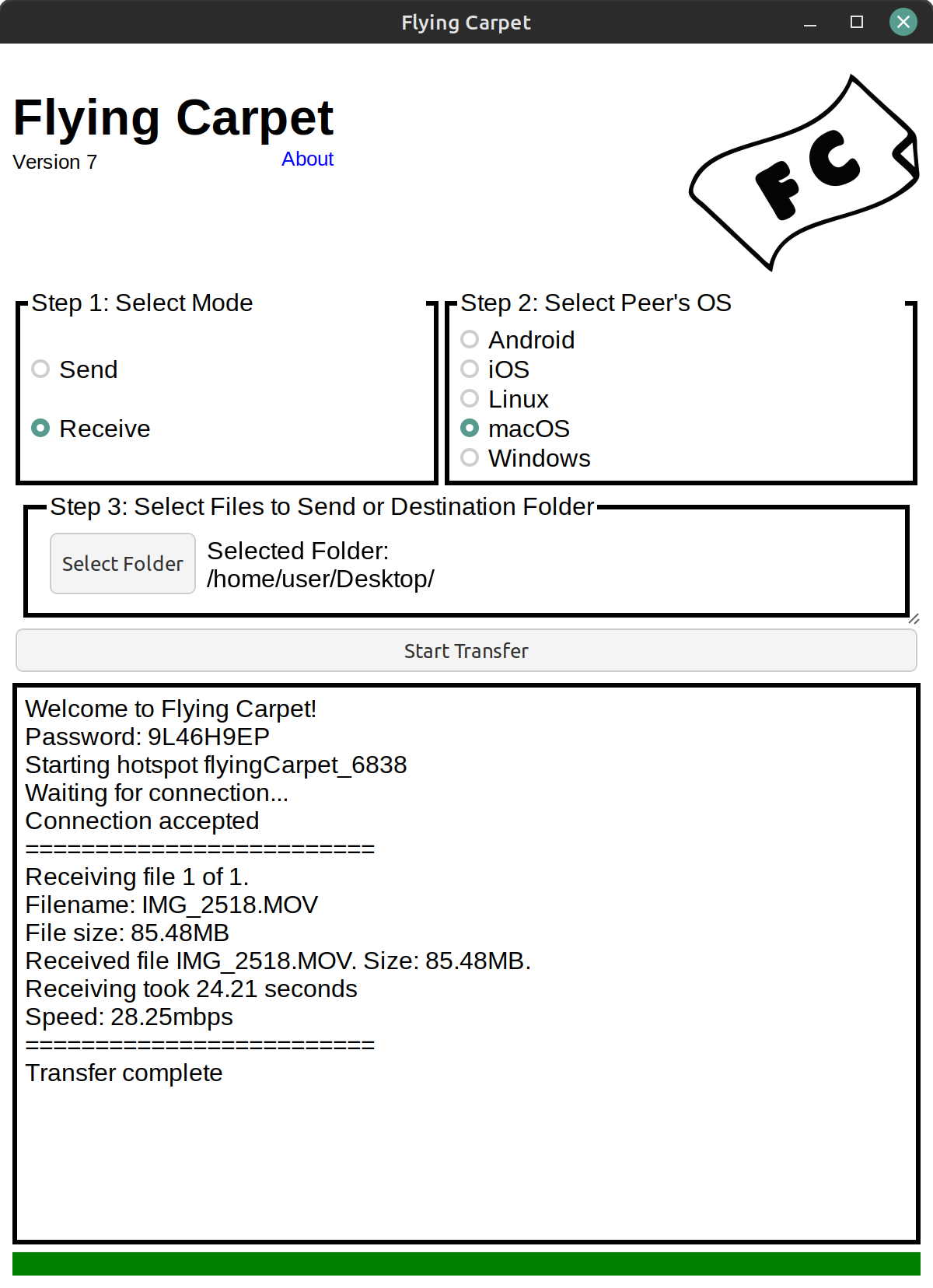
https://github.com/spieglt/FlyingCarpet Send and receive files between Android, iOS, Linux, macOS, and Windows over ad hoc WiFi. No shared network or cell connection required, just two devices with WiFi chips in close range. Don’t have a flash drive? Don’t have access to a wireless network? Need to move a file larger than 2GB between different filesystems
January 14, 2024By Prapattimynk
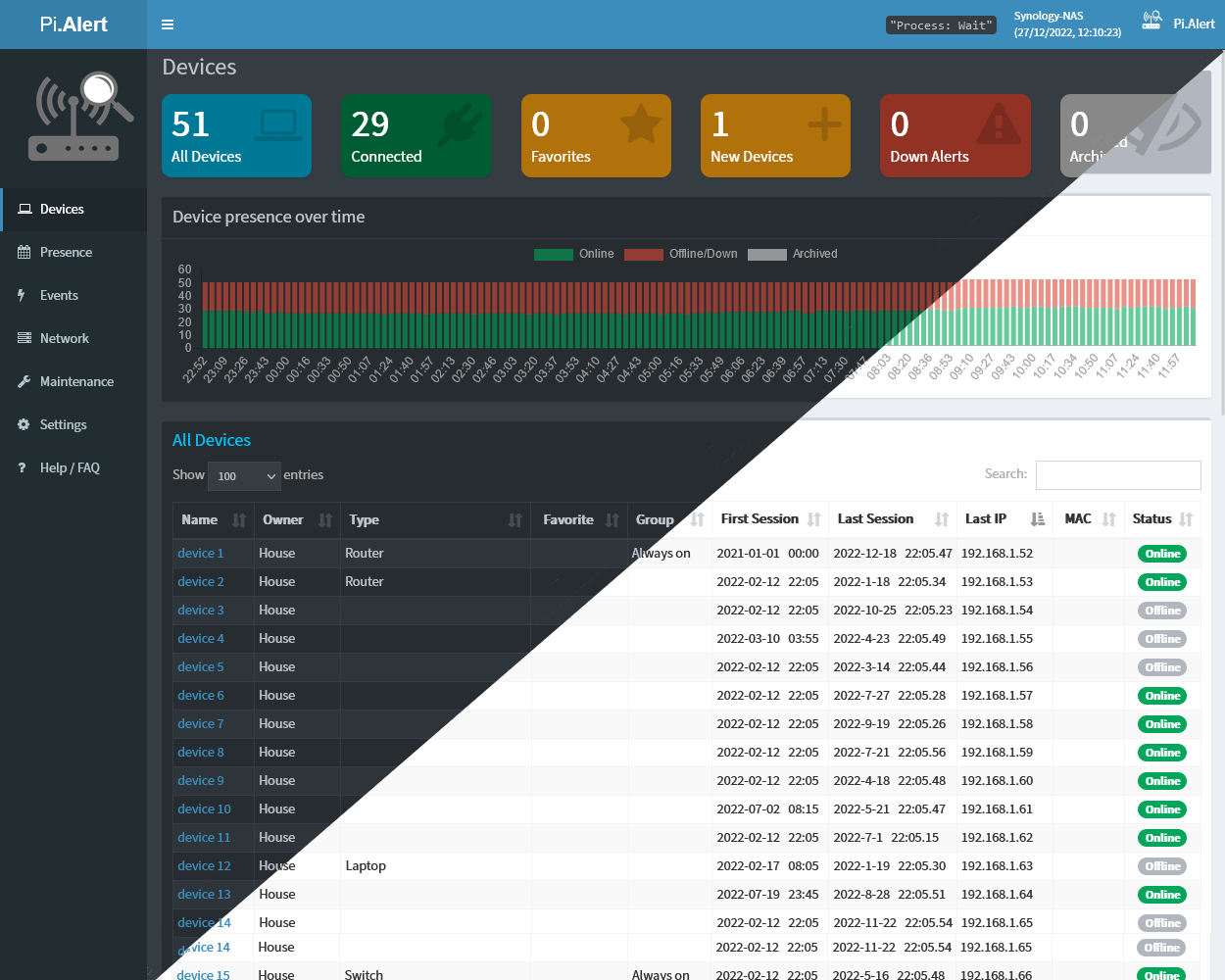
Get visibility of what’s going on on your WIFI/LAN network. Scan for devices, port changes and get alerts if unknown devices or changes are found. Write your own Plugins with auto-generated UI and in-build notification system. https://github.com/jokob-sk/Pi.Alert Why PiAlert❓ Most of us don’t know what’s going on on our home network, but we want our
January 14, 2024By Prapattimynk
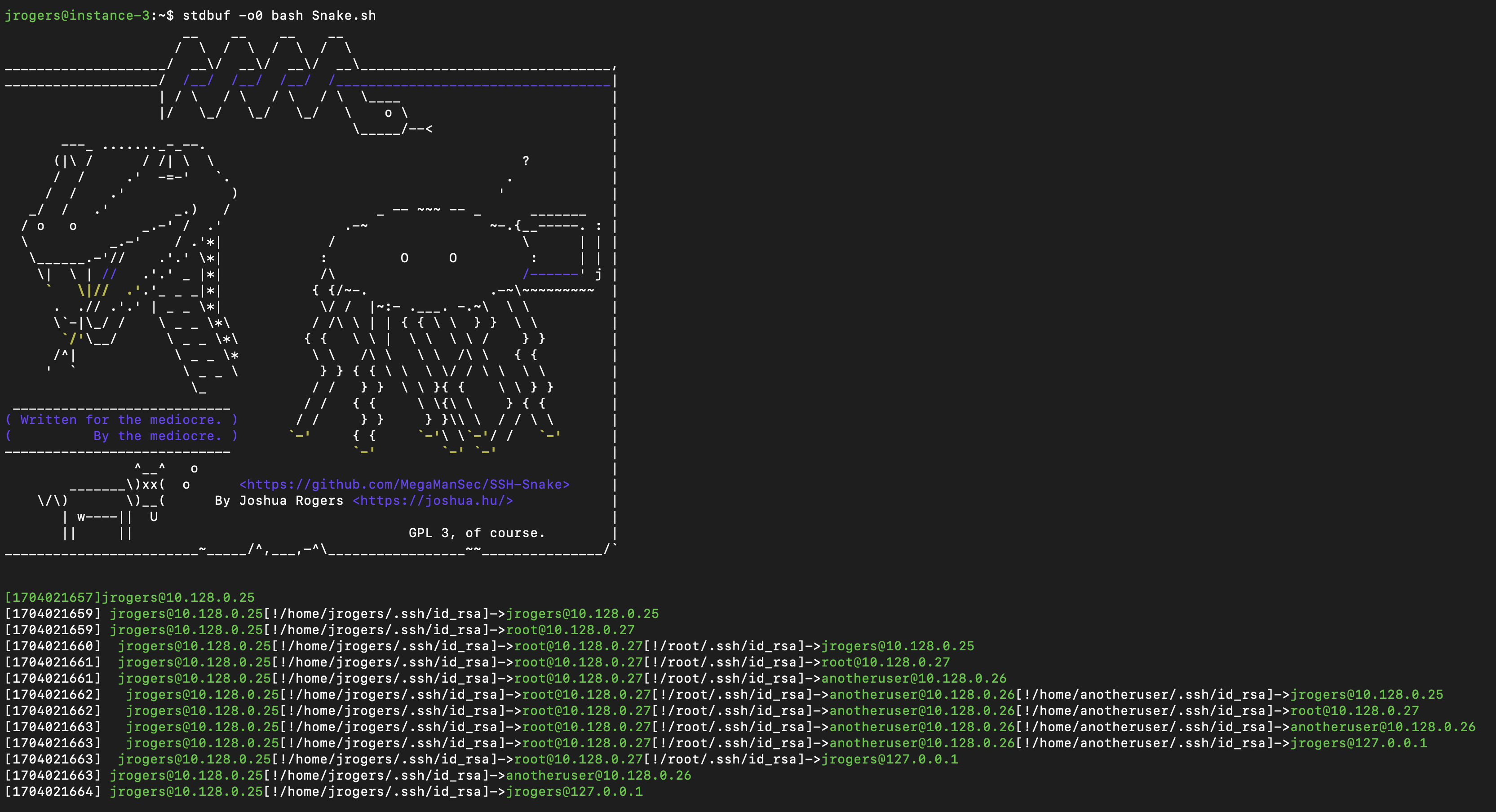
https://github.com/MegaManSec/SSH-Snake SSH-Snake is a powerful tool designed to perform automatic network traversal using SSH private keys discovered on systems, with the objective of creating a comprehensive map of a network and its dependencies to identify the extent that a network can be compromised using SSH and SSH private keys starting from a particular system. SSH-Snake
January 14, 2024By Prapattimynk
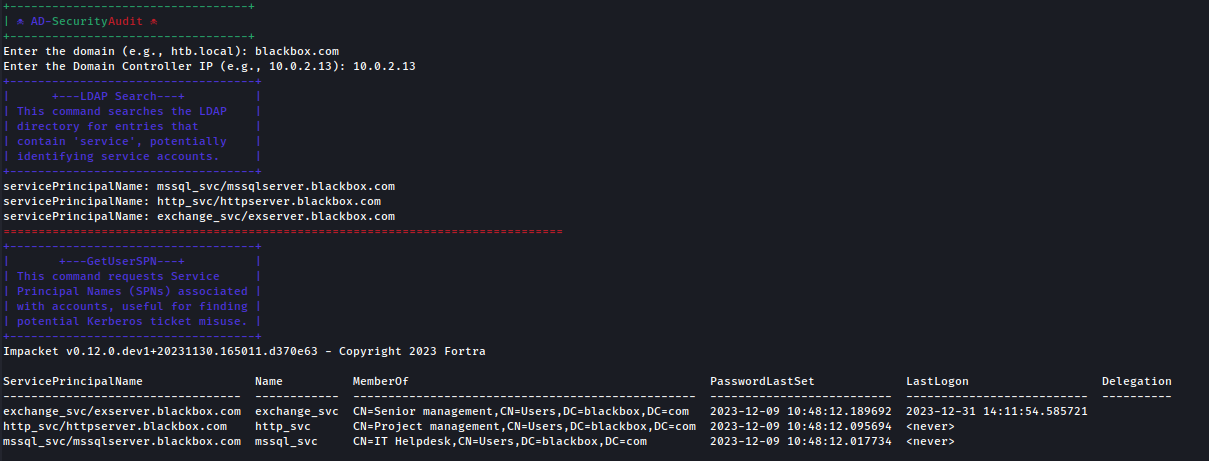
https://github.com/emrekybs/AD-AssessmentKit Contains a collection of Bash scripts designed for comprehensive security audits and network mapping of Active Directory (AD) environments. The scripts automate various tasks including LDAP querying, Kerberos ticket analysis, SMB enumeration, and exploitation of known vulnerabilities like Zerologon and PetitPotam. AD-SecurityAudit.sh Focuses on initial reconnaissance and vulnerability identification in AD domains, requiring only
January 14, 2024By Prapattimynk
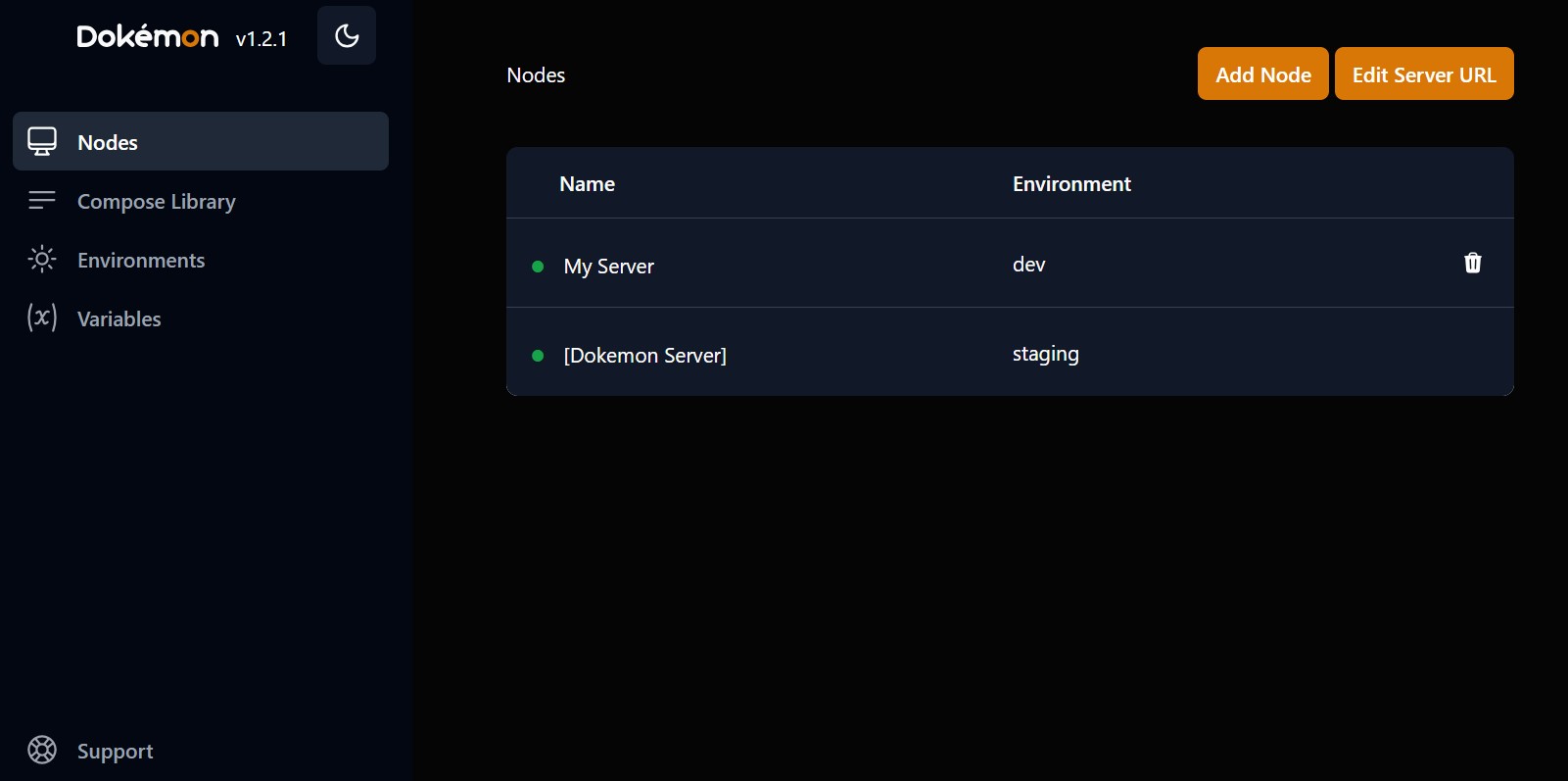
https://github.com/productiveops/dokemon Dokémon is a friendly GUI for managing Docker Containers. You can manage multiple servers from a single Dokemon instance. Check https://dokemon.dev for more details. Production Usage We recommend that you run Dokemon on a private network whenever possible. If you are running on a VPS with only public access, we recommend that you use an SSL
January 14, 2024By Prapattimynk
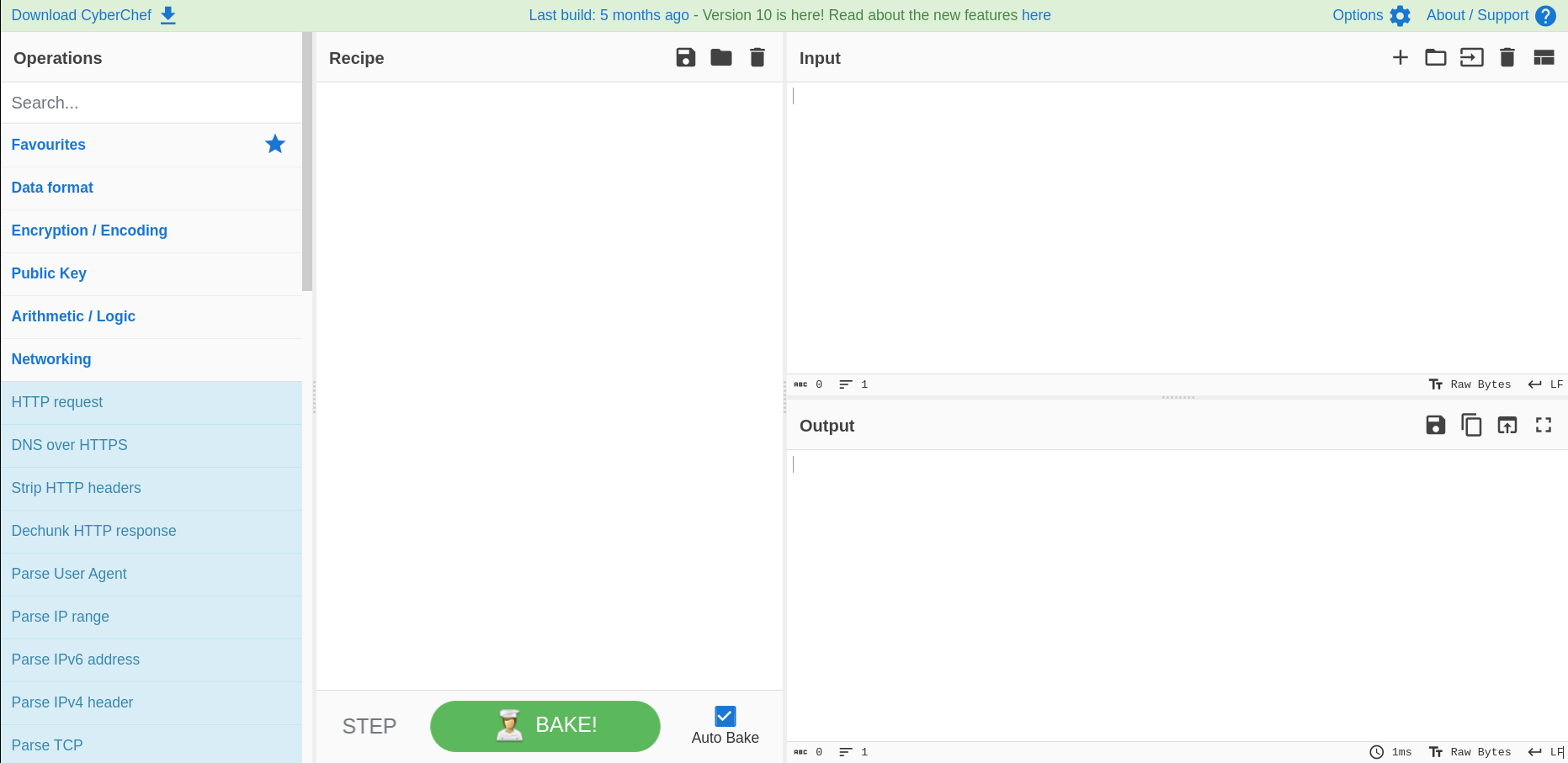
https://github.com/gchq/CyberChef https://gchq.github.io/CyberChef The Cyber Swiss Army Knife CyberChef is a simple, intuitive web app for carrying out all manner of “cyber” operations within a web browser. These operations include simple encoding like XOR and Base64, more complex encryption like AES, DES and Blowfish, creating binary and hexdumps, compression and decompression of data, calculating hashes and
January 14, 2024By Prapattimynk
https://github.com/akamai/ddspoof DDSpoof is a tool that enables DHCP DNS Dynamic Update attacks against Microsoft DHCP servers in AD environments. For additional information, please refer to our blog posts: For information on how to mitigate DDSpoofing attacks in your networks, please refer to Invoke-DHCPCheckup.ps1 Setup Usage Commandline arguments: At startup, DDSpoof will perform the following: After the