December 16, 2024By Prapattimynk
Improved Speed & Efficiency: Significantly faster and smoother DNS brute-forcing with lightweight resource usage. Memory & Resource Management: Optimized to handle large-scale DNS scans without consuming excessive system resources. Flexible Input: Supports both stdin and file-based domain lists for DNS brute-forcing. Concurrency Control: Rate limiting and concurrency management to ensure stable performance under heavy loads.
June 26, 2024By Prapattimynk
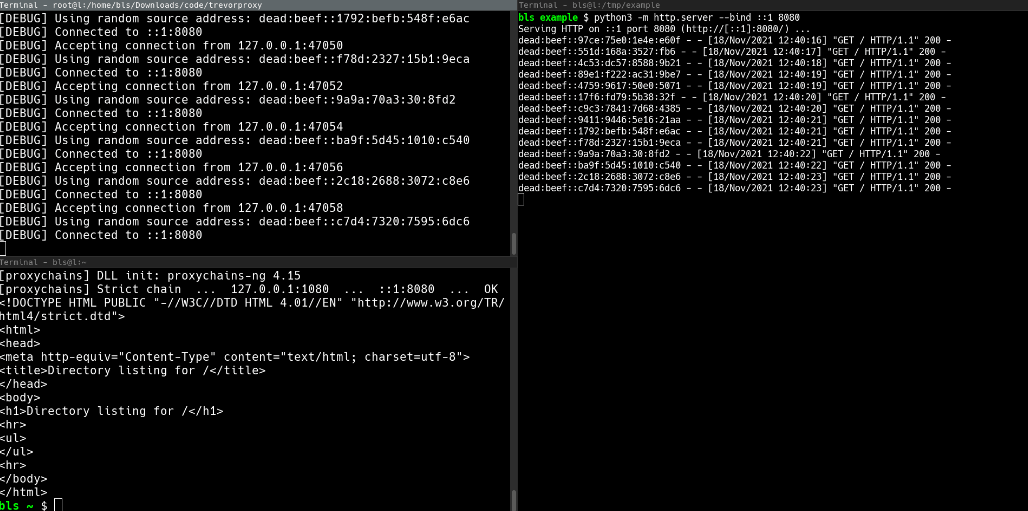
Installation pip install git+https://github.com/blacklanternsecurity/trevorproxy See the accompanying Blog Post for a fun rant and some cool demos! A SOCKS proxy written in Python that randomizes your source IP address. Round-robin your evil packets through SSH tunnels or give them billions of unique source addresses! TREVORproxy IPv6 Subnet Proxy Diagram TREVORproxy SSH Proxy Demo TREVORproxy Subnet
June 21, 2024By Prapattimynk
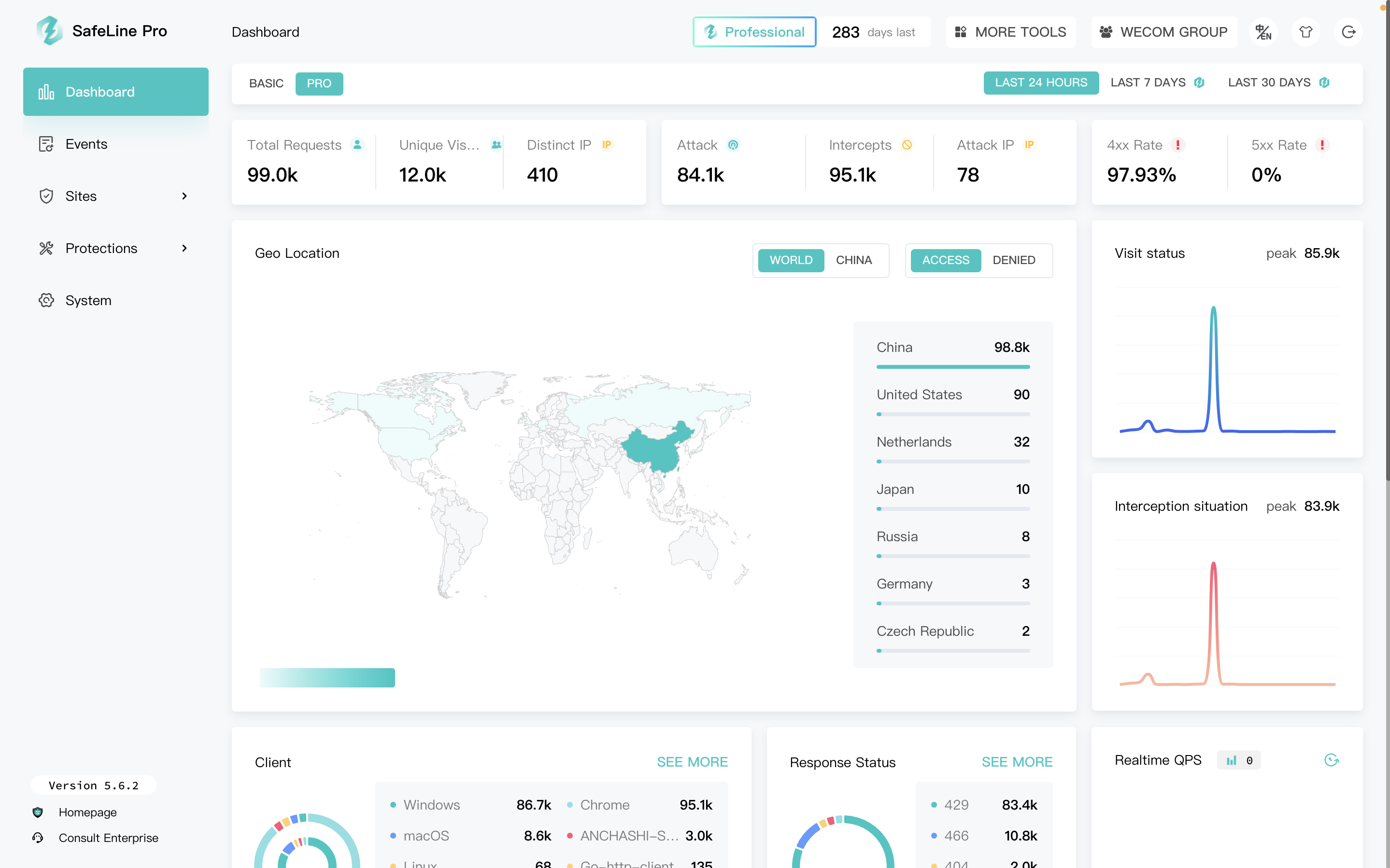
SafeLine is a web security gateway to protect your websites from attacks and exploits. It defenses for all of web attacks, such as sql injection, code injection, os command injection, CRLF injection, ldap injection, xpath injection, rce, xss, xxe, ssrf, path traversal, backdoor, bruteforce, http-flood, bot abused and so on. 🏠Home | 📖Documentation
June 21, 2024By Prapattimynk
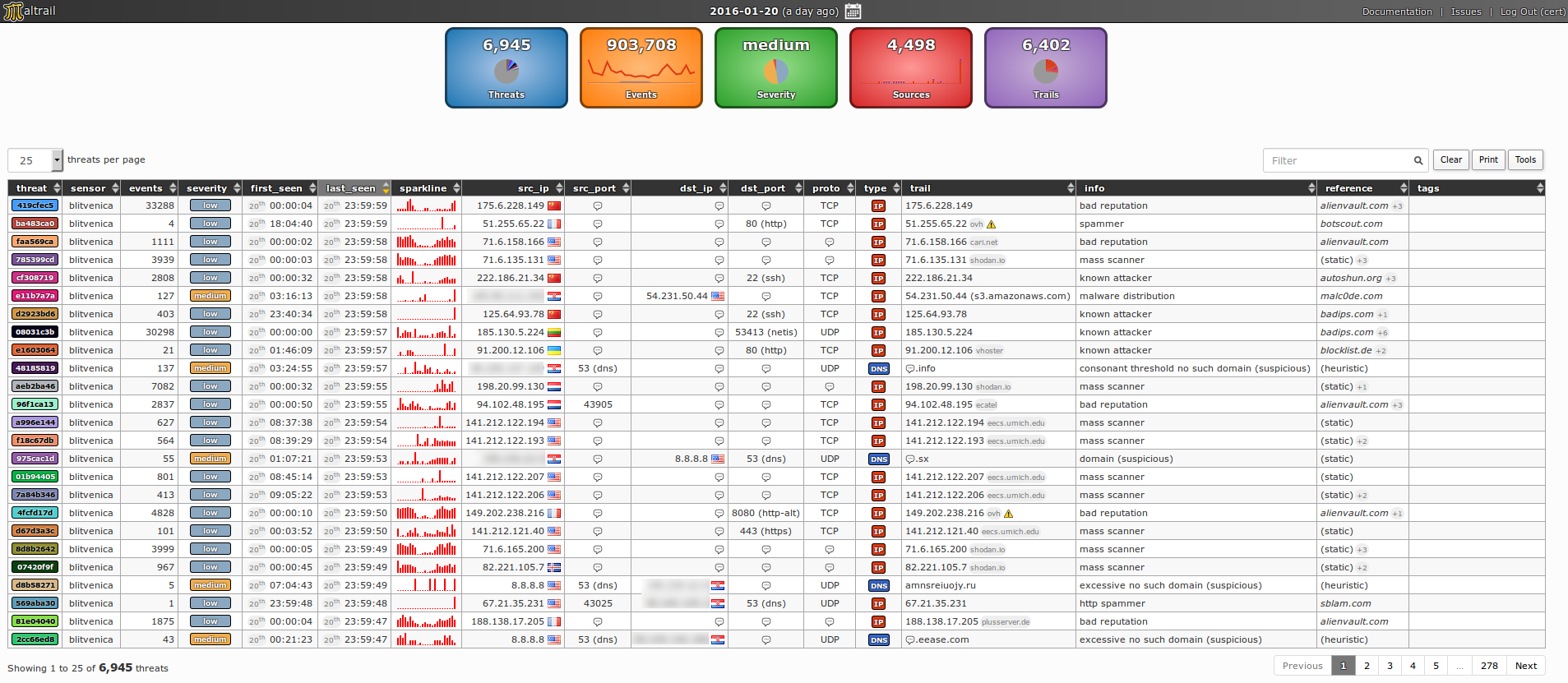
Content Introduction Architecture Demo pages Requirements Quick start Administrator’s guide Sensor Server User’s guide Reporting interface Real-life cases Mass scans Anonymous attackers Service attackers Malware Suspicious domain lookups Suspicious ipinfo requests Suspicious direct file downloads Suspicious HTTP requests Port scanning DNS resource exhaustion Data leakage False positives Best practice(s) License Sponsors Developers Presentations Publications Blacklist
April 27, 2024By Prapattimynk
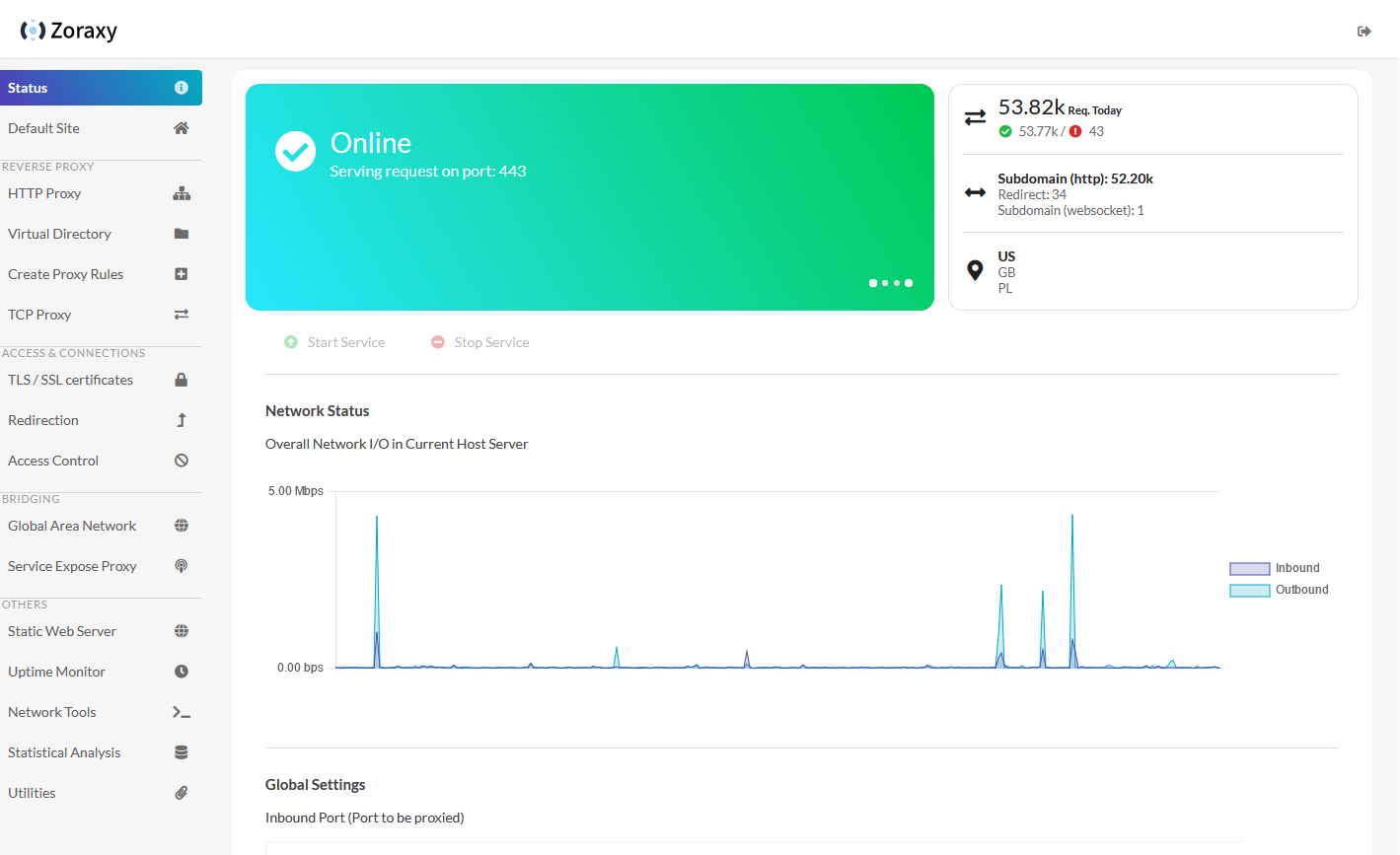
https://github.com/tobychui/zoraxy General purpose request (reverse) proxy and forwarding tool for networking noobs. Now written in Go! Zoraxy v3 HTTP proxy config is not compatible with the older v2. If you are looking for the legacy version of Zoraxy, take a look at the v2 branch Features Downloads Windows /Linux (amd64) /Linux (arm64) For other systems or architectures, please
April 4, 2024By Prapattimynk
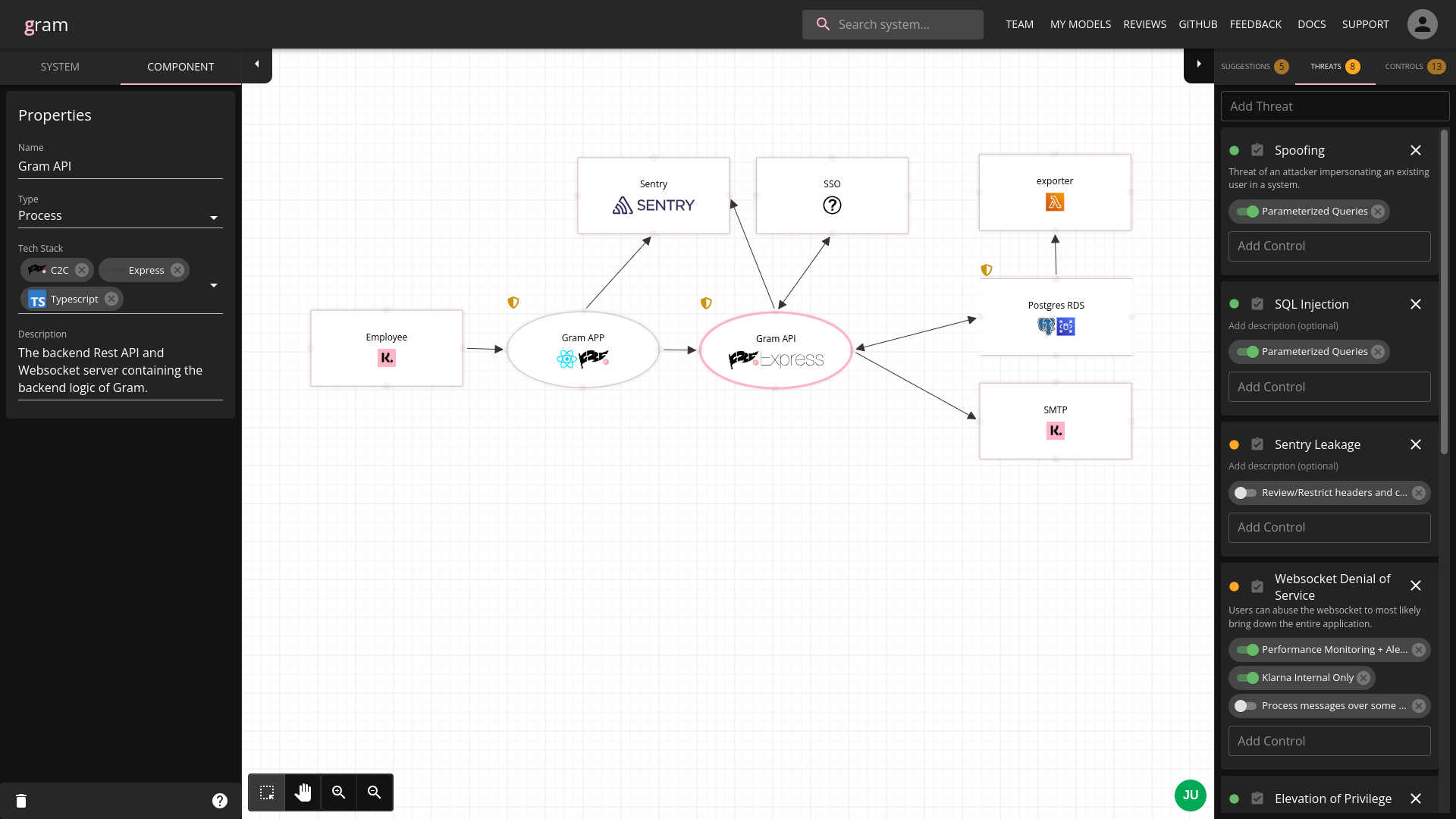
https://github.com/klarna-incubator/gram Gram is Klarna’s own threat model diagramming tool developed internally by Klarna’s Secure Development team. It is a webapp for engineers to collaboratively create threat models for their systems, providing a easy-to-understand way to document a system as a dataflow diagram with threats/controls attached. Features ✨ Getting Started 🚀 See Quick Start.
March 26, 2024By Prapattimynk
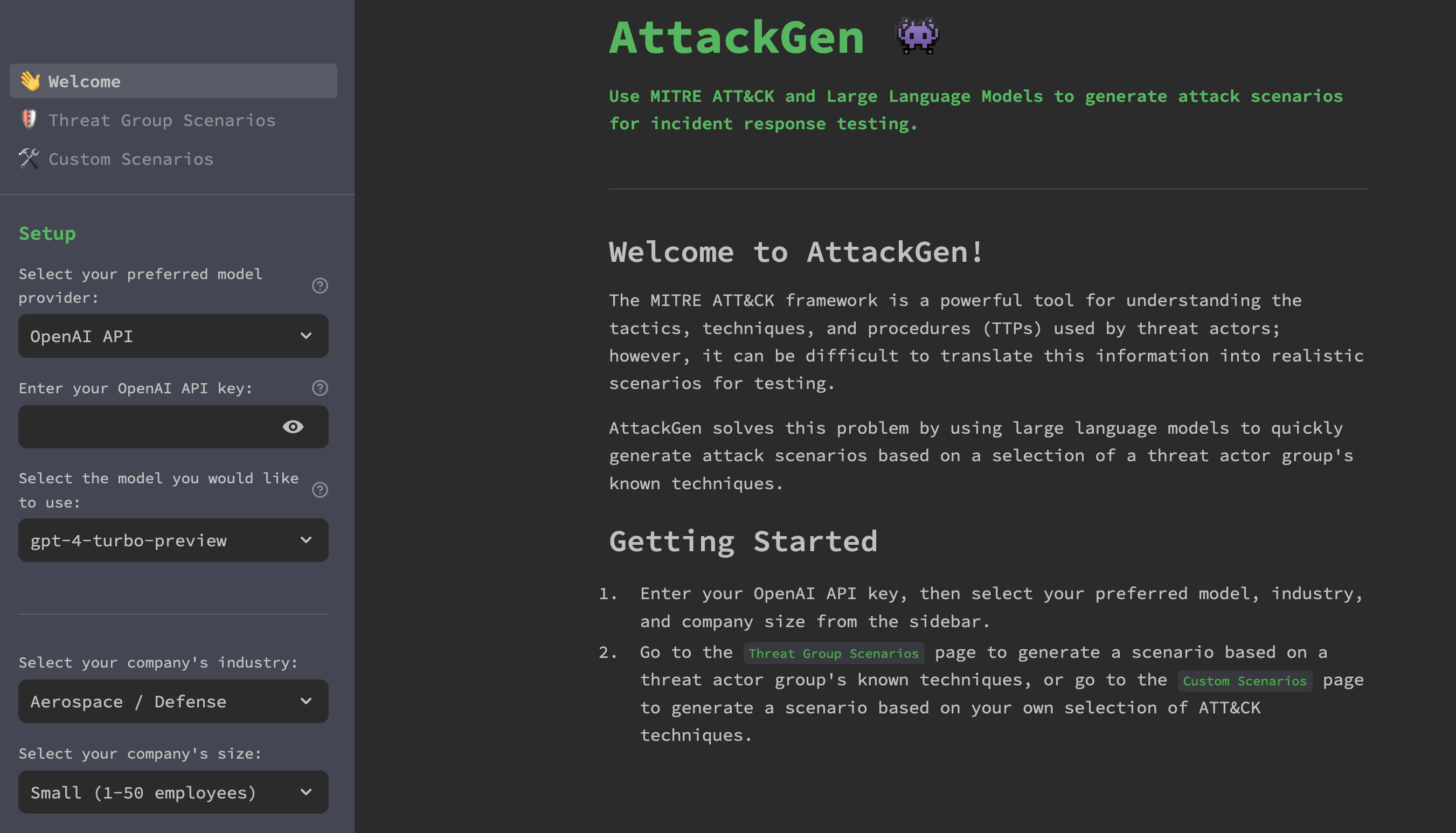
https://github.com/mrwadams/attackgen AttackGen is a cybersecurity incident response testing tool that leverages the power of large language models and the comprehensive MITRE ATT&CK framework. The tool generates tailored incident response scenarios based on user-selected threat actor groups and your organisation’s details. Features Requirements Installation Option 1: Cloning the Repository Option 2: Using Docker LangSmith Setup If
March 20, 2024By Prapattimynk
Introduction Are you interested in enhancing the capabilities of your rooted device? If so, you might want to consider installing Kali NetHunter. Kali NetHunter is an Android penetration testing platform that allows you to use various tools and techniques to assess the security of your network. In this guide, we will walk you through the
January 14, 2024By Prapattimynk
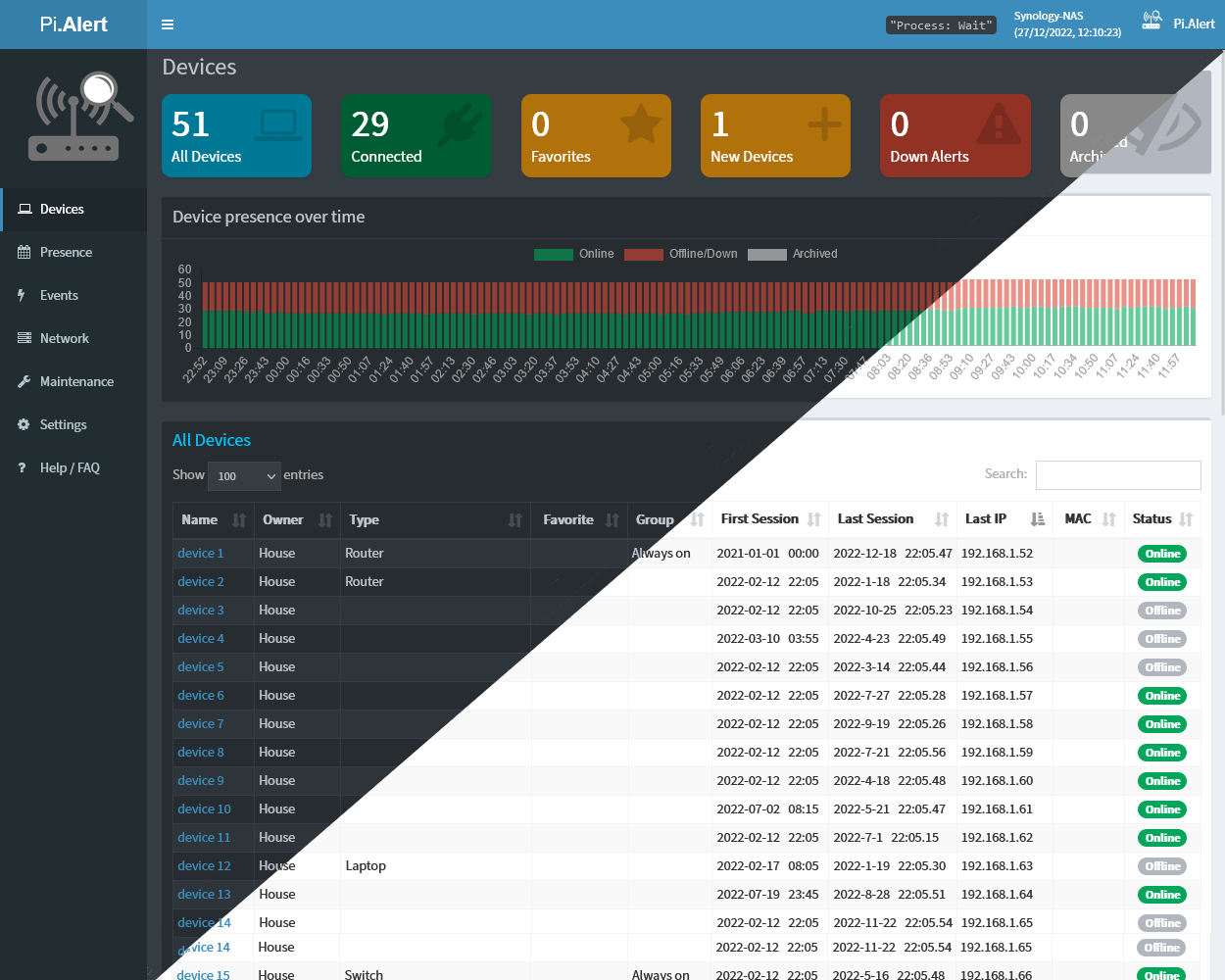
Get visibility of what’s going on on your WIFI/LAN network. Scan for devices, port changes and get alerts if unknown devices or changes are found. Write your own Plugins with auto-generated UI and in-build notification system. https://github.com/jokob-sk/Pi.Alert Why PiAlert❓ Most of us don’t know what’s going on on our home network, but we want our